Transit Gateway BGP over LAN in AWS Workflow
Introduction
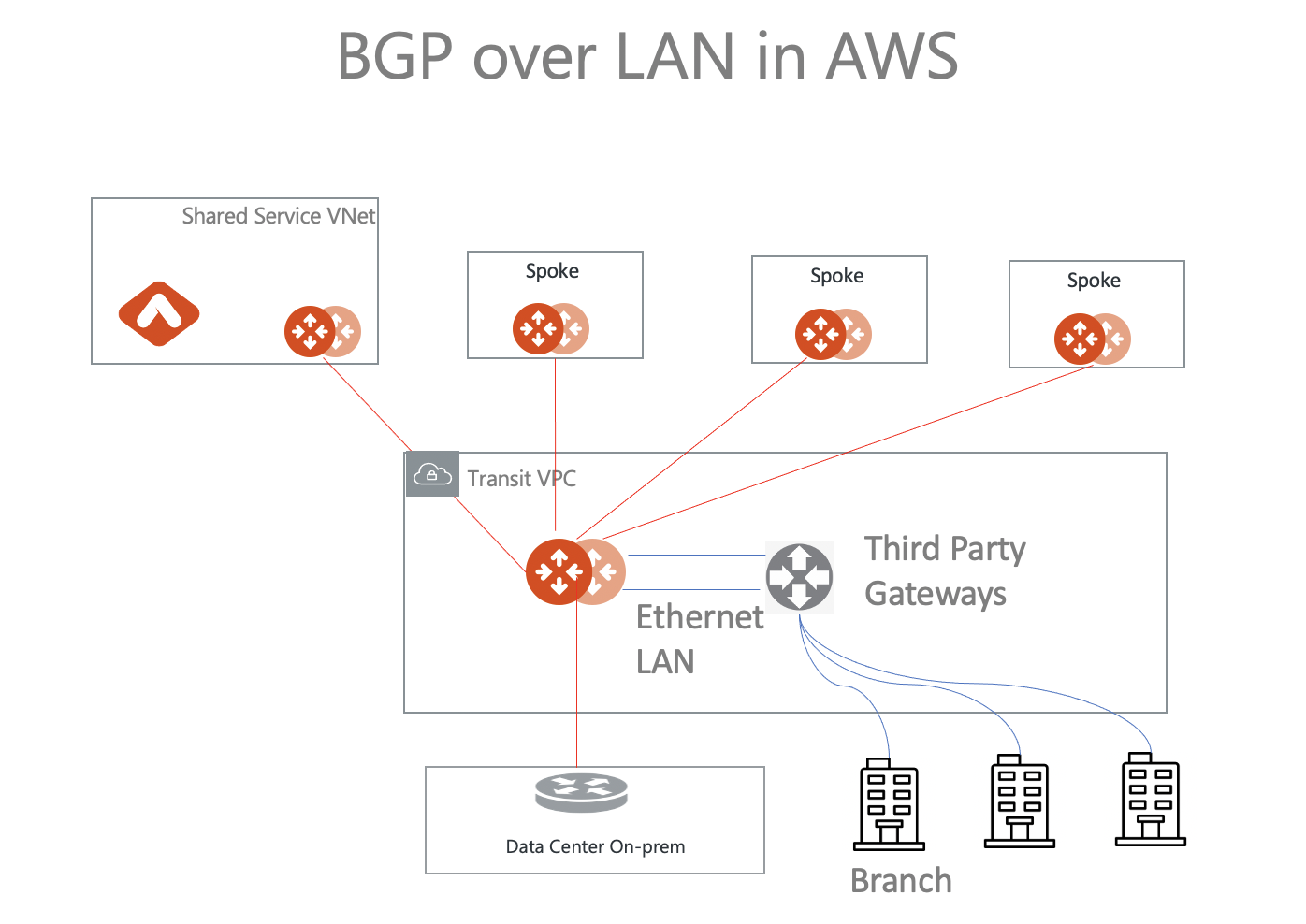
Transit BGP to LAN allows Aviatrix Transit Gateways to communicate with a pair of instances in the same VPC in AWS without running any tunneling protocol such as IPsec or GRE. One use case is to interoperate with third-party virtual appliances such as SD-WAN cloud instances that do not have the capability to support BGP over any tunneling protocols.
For example, integrating with SD-WAN gateways can be deployed as below, where an Aviatrix Multicloud Transit Gateway connects to a third-party cloud instance in the same VPC in AWS.
This document describes a step-by-step instruction on how to build Aviatrix Transit Gateway to External Device using BGP over LAN in AWS.
For other BGP over LAN workflows, please see:
For more information about Multicloud Transit Network and External Device, please see:
|
The key ideas for this solution are:
-
A BGP session is established between a third-party cloud instance and an Aviatrix Transit Gateway via each LAN interface in the same VPC.
-
Data plane traffic also runs between a third-party cloud instance and Aviatrix Transit Gateway via each LAN interface without a tunnel protocol such as IPsec and GRE.
Prerequisites
-
Upgrade Aviatrix Controller to at least version 6.3.
-
In this example, you are going to deploy the below VPCs in AWS:
-
Transit VPC (i.e. 10.1.0.0/16) by utilizing Aviatrix feature Create a VPC with Aviatrix FireNet VPC option enabled.
-
Spoke VPCs (i.e. 192.168.1.0/24 and 192.168.2.0/24) by utilizing Aviatrix feature Create a VPC as the previous step or manually deploying it in each cloud portal. Moreover, feel free to use your existing cloud network.
-
-
Third-party cloud instance supports high throughput.
Deploying the Aviatrix Multicloud Transit Solution
Refer to Global Transit Network Workflow Instructions for the below steps. Please adjust the topology depending on your requirements.
-
Deploy the Aviatrix Multicloud Transit Gateway and HA with High Performance Encryption Mode enabled. In this example, size c5n.4xlarge is selected to benchmark performance.
-
Deploy a Spoke Gateway and HA to launch Aviatrix Spoke gateway and enable HA with High Performance Encryption Mode enabled in Spoke VPC. In this example, size c5n.4xlarge is selected to benchmark performance.
Launching Third-Party Cloud Instances
Deploy third-party cloud instances in the same VPC where the Aviatrix Transit Gateways are located.
-
Create a third-party cloud instance and put the MGMT interface in the public gateway subnet.
-
Create a new public WAN subnet and a dedicated routing table for the WAN interface if needed.
-
Create a new private LAN subnet and a dedicated routing table (optional) for the LAN interface.
-
Make sure the function "Source/Dest check on third-party cloud instance’s interfaces" is disabled.
|
The primary Aviatrix Transit Gateway must be deployed in the same Available Zone (AZ) as the first third-party cloud instance. The HA Transit Gateway if deployed must reside in the same AZ as the second cloud instance. |
Building BGP over LAN
Configure BGP over LAN on the Aviatrix Transit Gateway.
-
In CoPilot, go to Networking > Connectivity > External Connections (S2C).
-
Click External Connection.
-
In the Add External Connection dialog, select External Device and BGP over LAN.
-
Enter the following information in the fields.
Setting Value Transit VPC Name
Select the Transit VPC ID where Transit GW was launched
Connection Name
Provide a unique name to identify the connection to external device
Aviatrix Transit Gateway BGP ASN
Configure a BGP AS number that the Transit GW will use to exchange routes with external device
Primary Aviatrix Transit Gateway
Select the Transit GW
Enable Remote Gateway HA
Check this option in this example to connect two external devices
Remote BGP AS Number
Configure a BGP AS number that third-party cloud primary instance will use to exchange routes with Aviatrix Transit Primary
Remote LAN IP
Use the private IP of the LAN interface of the third-party cloud primary instance
Local LAN IP
Leave it blank and the Controller will assign an IP in the same subnet as the Remote LAN IP. Optionally configure an IP of your choosing within the same subnet of the Remote LAN IP.
Remote BGP AS Number (Backup)
Configure a BGP AS number that the third-party cloud HA instance will use to exchange routes with Aviatrix Transit HA.
Remote LAN IP (Backup)
Use the private IP of the LAN interface of the third-party cloud HA instance.
Local LAN IP (Backup)
Leave it blank and the Controller will assign an IP in the same subnet as the Remote LAN IP (Backup). Optionally configure an IP of your choosing within the same subnet as the Remote LAN IP (Backup).
-
Click Save to generate BGP session over LAN.
Downloading the BGP over LAN configuration
-
On the External Connections (S2C) tab, click the vertical ellipsis
 and select Download Configuration.
and select Download Configuration. -
Select the Vendor type, Platform, and Software.
-
Click Download.
Configuring BGP over LAN on Third-Party Cloud Instance
-
Open the downloaded BGP over LAN configuration file.
-
Configure the related BGP and LAN settings in the third-party cloud instance.
Verifying the LAN Connection Status
You can check the tunnel status by going to Diagnostics > Cloud Routes > External Connections and checking the Tunnel Status column for the external connection.
Verifying the BGP Session Status
You can check the BGP Session status by going to Diagnostics > Cloud Routes > BGP Info. The Status should be Established. If some external connections for the selected Transit Gateway are Not Established, the overall BGP Status for the Transit Gateway is Partially Established.
Ready to Go
At this point, run connectivity and performance tests to ensure everything is working correctly. You can do this with the Diagnostic Tools.