Distributed Cloud Firewall Setup and Default Action Rule
Distributed Cloud Firewall (DCF) provides advanced traffic management capabilities to enforce zero trust principles across your network. This document focuses on enabling the DCF feature and configuring the Default Action Rule, ensuring secure and consistent traffic handling in the absence of explicit rules.
|
If you configured the ThreatIQ and/or Geoblocking features prior to Controller version 7.2.4820, in 7.2.4820 you automatically receive a free Distributed Cloud Firewall (DCF) license. If you did not configure the ThreatIQ and/or Geoblocking features prior to Controller version 7.2.4820, you are expected to purchase a DCF license. This will include the ExternalGroup feature (replaces the ThreatIQ and Geoblocking features). |
Enabling the Distributed Cloud Firewall Feature
Enabling the Distributed Cloud Firewall feature allows you to create and manage rules, rulesets, and policies to enforce zero trust principles.
| If you enabled Distributed Cloud Firewall in a previous Controller version, you do not need to enable it again. |
To enable the Distributed Cloud Firewall (DCF) feature, if it is not enabled already:
-
Go to the Security > Distributed Cloud Firewall > Policies tab.
-
Click Begin Using Distributed Cloud Firewall.
-
Click Begin again to confirm the action and enable the feature.
Default Action Rule for Distributed Cloud Firewall
|
Starting with Controller version 8.1, the Default Action Rule is automatically created when DCF is enabled. Legacy rules such as Greenfield and DefaultDenyAll are no longer generated; the Default Action Rule replaces their function. The Default Action Rule cannot be deleted. When you upgrade to Controller 8.1 or earlier, the existing DefaultDenyAll rule is converted to a non-system rule, which you can delete. If you use Controller 8.0 or earlier, both a Greenfield Rule and a DefaultDenyAll rule are deleted. |
After enabling the Distributed Cloud Firewall feature, a Default Action Rule is created. This is a system rule used to enforce zero trust principles by controlling how traffic is handled in the absence of explicit rules. This rule must be set to Deny after it is created, to ensure that traffic is not permitted by default. The action of the Default Action Rule is enforced globally; it is part of the broader policy evaluation framework and is evaluated after all user-defined and system-defined rules/rulesets.
| You may see the Manage Rules Better with Rulesets splash screen when you first access the Policies tab. If so, click Acknowledge to continue. |
New DCF Users
-
On the Security > Distributed Cloud Firewall > Policies tab, click Begin Using Distributed Cloud Firewall.
You may have to click Begin again to confirm the action. This Default Action Rule is then created on the Policies tab in the User Ruleset (formerly the V1 Policy List ruleset).
-
Change the action of the Default Action Rule to Deny. This is mandatory.
-
Continue with creating DCF rulesets and rules.
Existing DCF Users
-
On the Security > Distributed Cloud Firewall > Policies tab, click Acknowledge on the splash screen that informs you about the Default Action Rule.
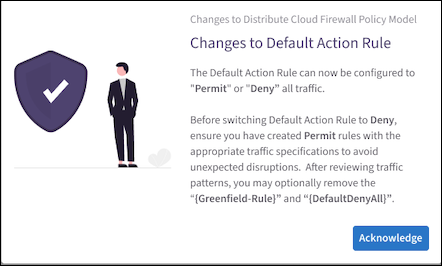
The Default Action Rule is displayed on the Policies tab in the V1 Policy List ruleset. The Default Action Rule replaces the pre-existing DefaultDenyAll rule, if you used the DCF feature prior to Controller 8.1. You can delete the old DefaultDenyAll rule if it exists.
-
Change the action of the Default Action Rule to Deny.
-
You can delete the pre-existing Greenfield-Rule if it exists, assuming that you have reviewed traffic patterns first.
Greenfield Rule and DefaultDenyAll Rule
In Controller 8.0 and lower, the placeholder Greenfield Rule prevents traffic from being dropped before you start configuring the rest of your rules. After you create additional rules you can move the Greenfield Rule where needed in your rule priority list. You can edit or delete the Greenfield Rule later, if desired.
| The Greenfield Rule is only enforced on gateways, and not on Security Groups in the cloud. |
By default (if you selected the recommended Permit All Traffic option), the Greenfield Rule has the following attributes:
-
Source/Destination Groups: Anywhere (0.0.0.0/0)
-
Protocol: Any
-
Action: Permit
-
Logging: On
The DefaultDenyAll Rule blocks traffic to any CIDR covered in Distributed Cloud Firewall rules. This rule is not editable.
DCF-Related Features
If the Distributed Cloud Firewall feature is enabled, these features are available:
-
Enforcement on PSF Gateways
-
Enforcement on External Connections
-
Enforcement on Transit Egress
You must enable these features from the Security > Distributed Cloud Firewall > Settings tab. With these features, you can enforce DCF on PSF Gateways, External Connections, or Transit Egress gateways.
-
DCF on Kubernetes Clusters from the Feature Previews list. To use this feature, you must enable it from the Discovery of Kubernetes Resources card on the Groups > Settings tab.