Deploy Check Point instance From AWS marketplace
-
Go to aws.amazon.com/marketplace and search for the chosen instance model/version in AWS Marketplace. Click Continue to Subscribe.
-
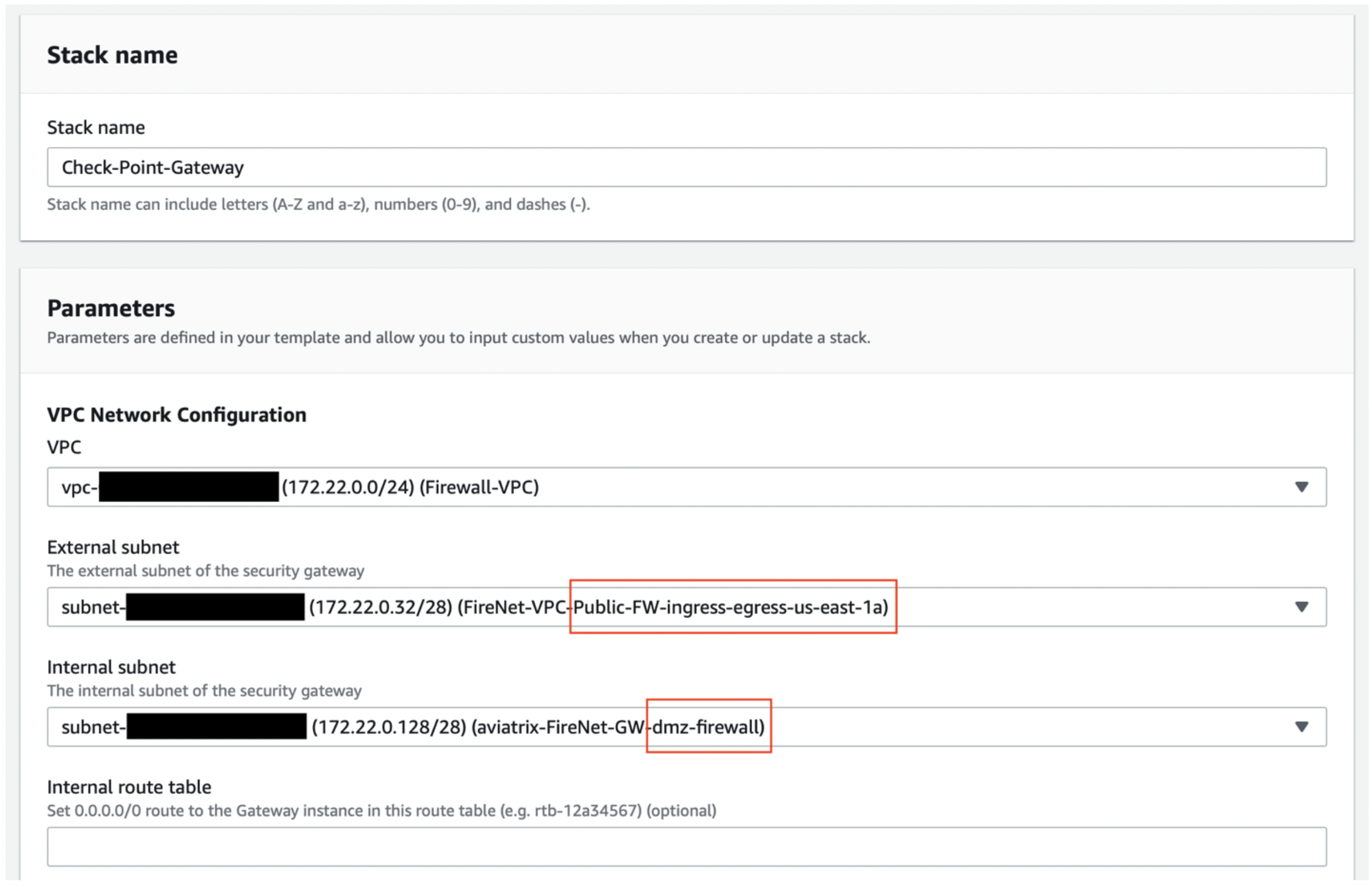
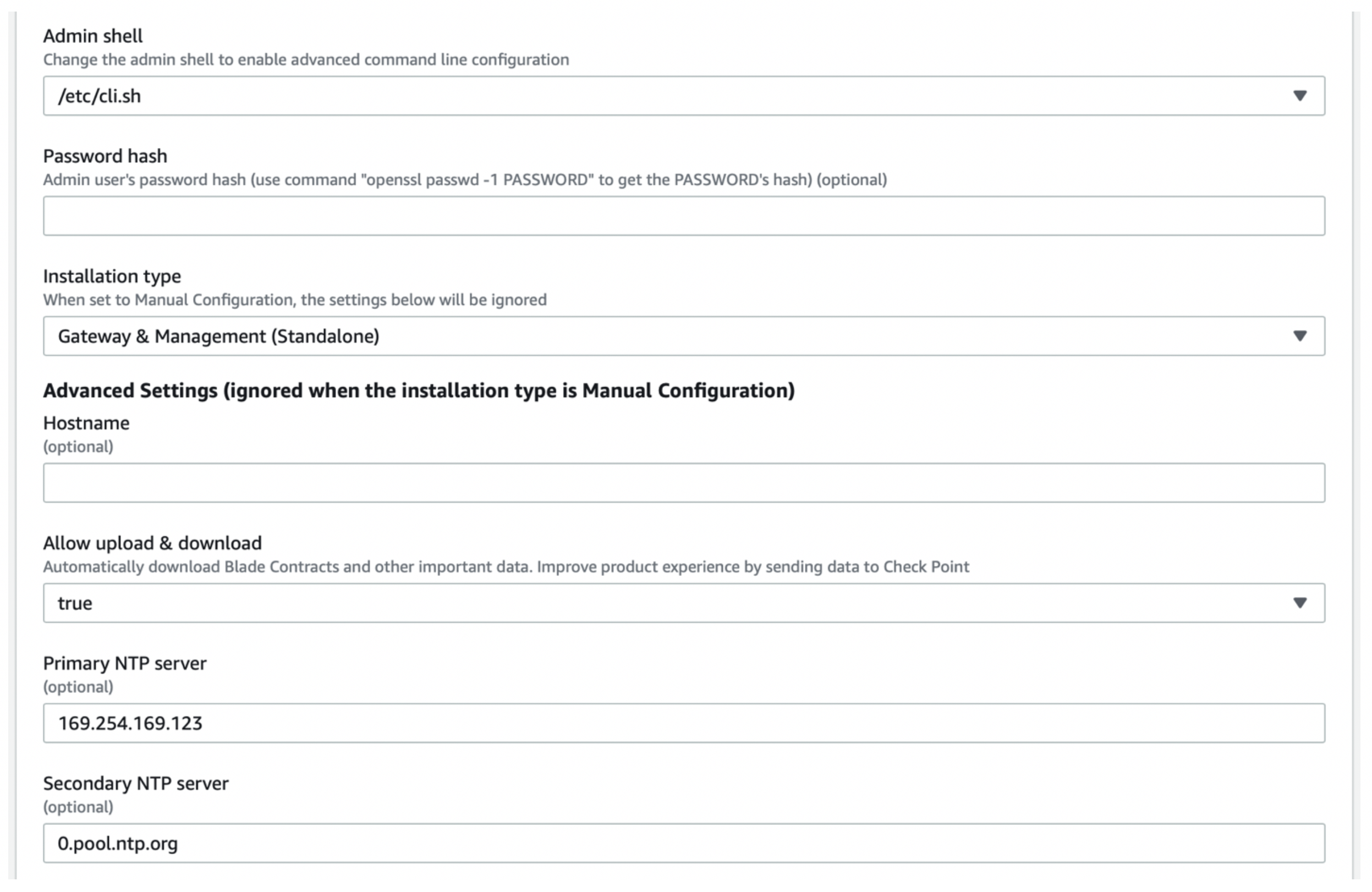
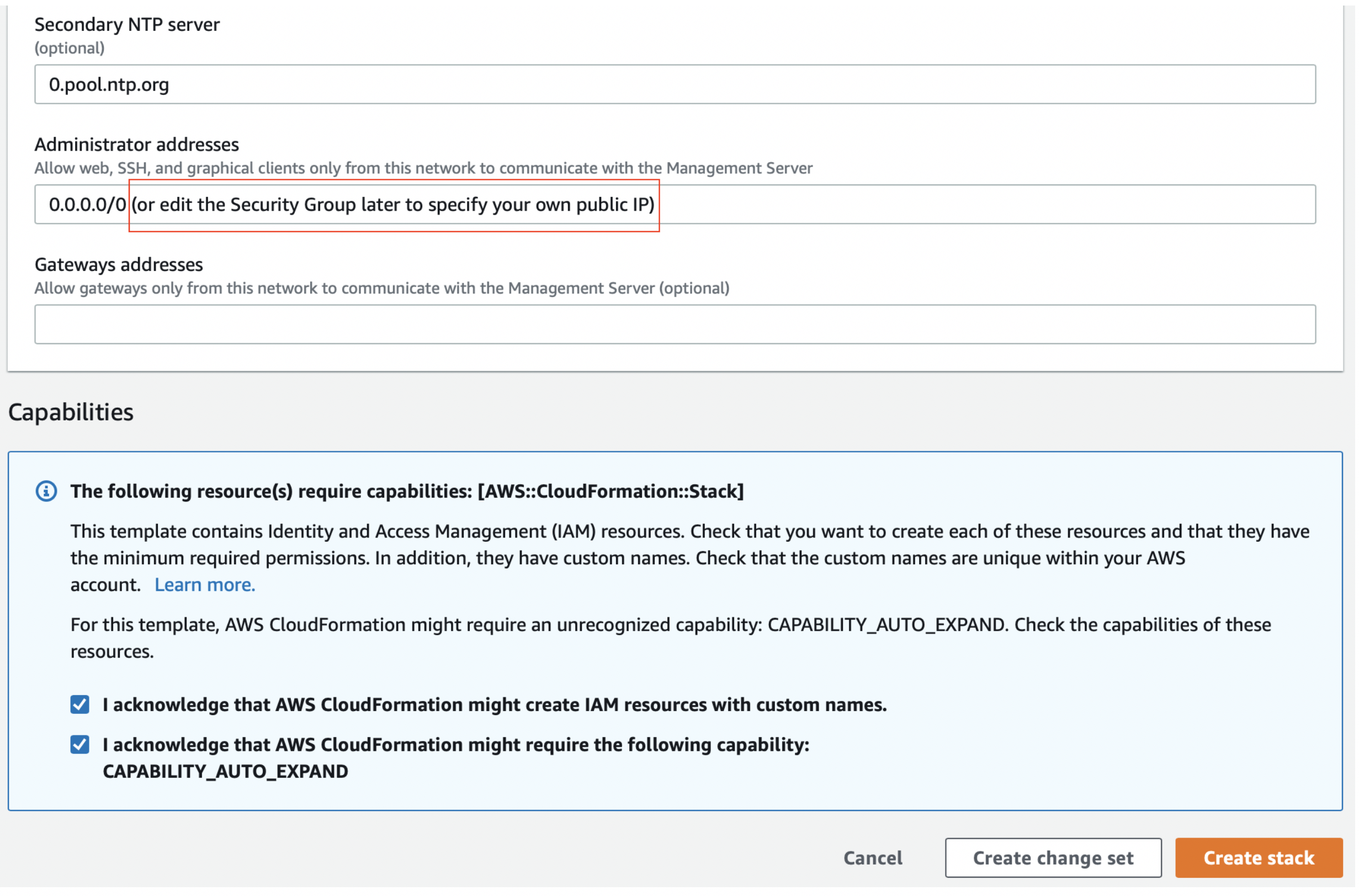
On the next screen, accept the terms and you should be able to continue. If you have chosen any of the R80 versions, you should be able to launch it using one of the CloudFormation templates. For the purpose of this guide, we are going to use template 15 (standalone into existing VPC). If you have a Management Server deployed already you should use template 2 instead.
-
This template will configure the first interface (eth0) as “external” and the second (eth1) as “internal”. For consistency purposes we suggest keeping eth0 as egress and management and eth1 for LAN.
-
The template should look like this (if you have selected existing VPC). Please make sure your interfaces are in the same AZ.
-
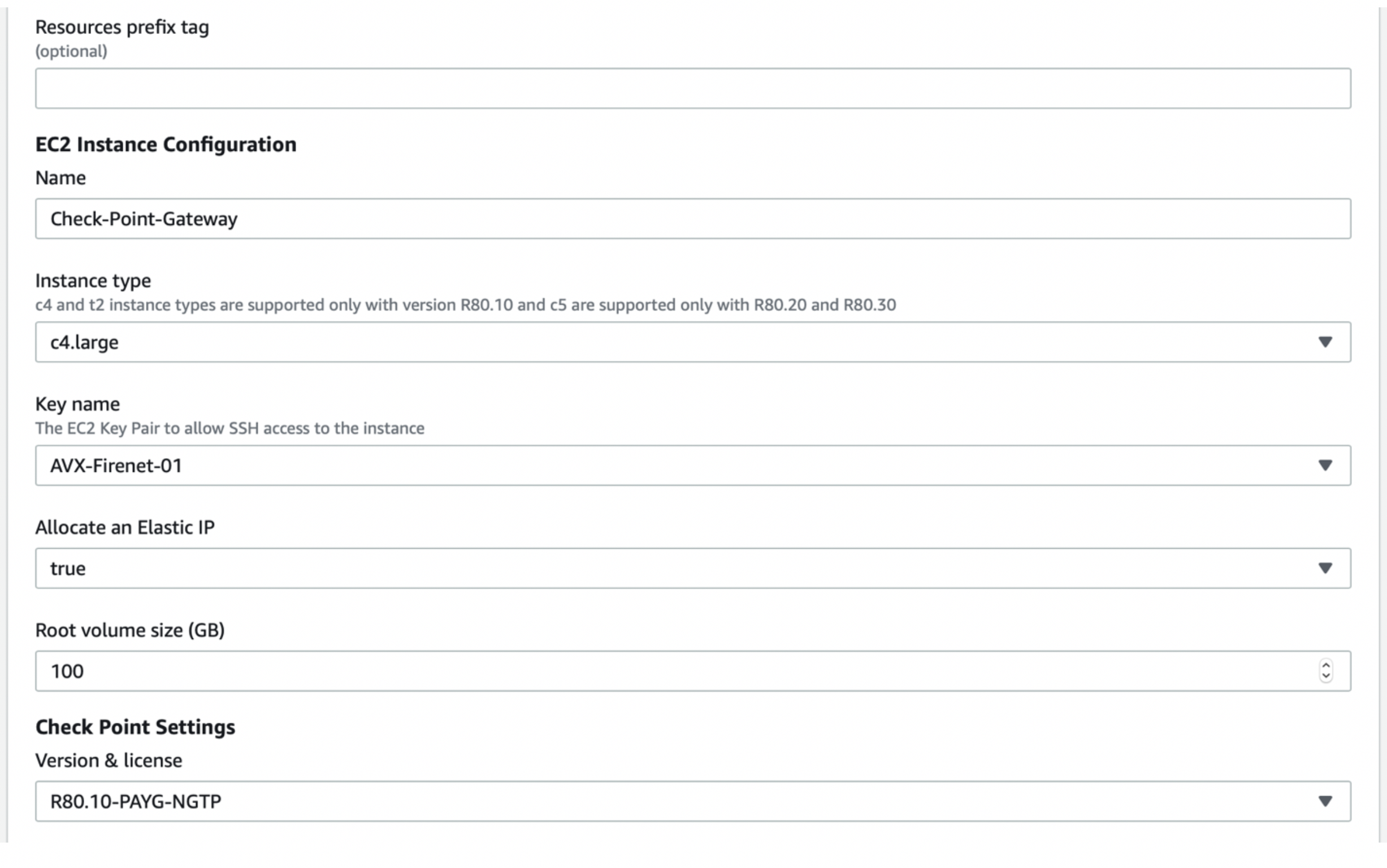
For the next part of the template, please make sure you have created/downloaded your pem key, as well as selected the proper instance size.For information on the networking features of each instance type, we recommend the following link.
-
After you click on Create stack you should go to CloudFormation to monitor the stack creation. Once the status is set to “CREATE_COMPLETE” you should be able to move on. Any different warning can be troubleshooted by checking the details in the “Outputs” tab are they are usually self-explanatory.
-
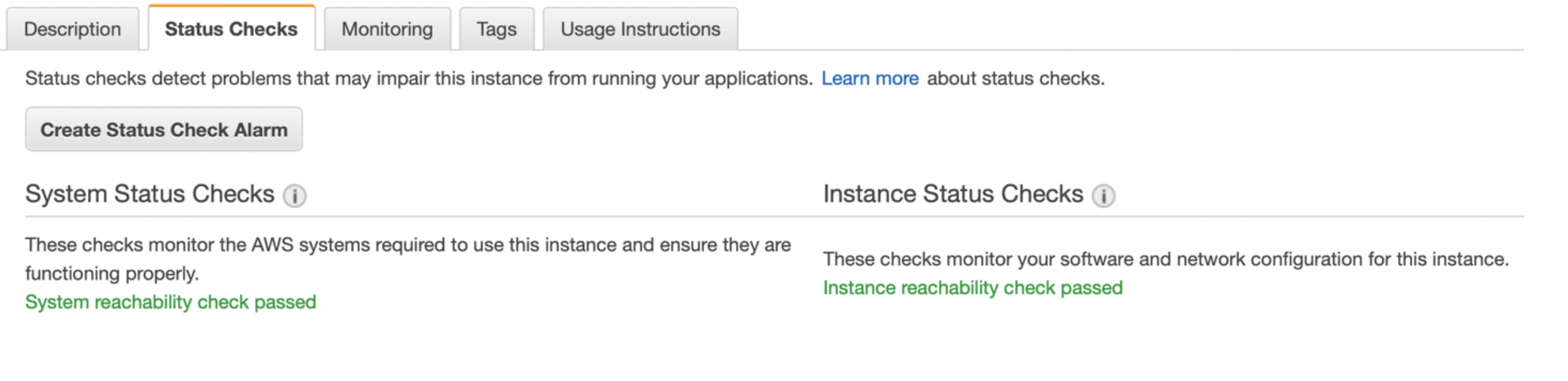
Now go to the EC2 instances to monitor the status check – once they are done, you should be able to SSH into the instance.
-
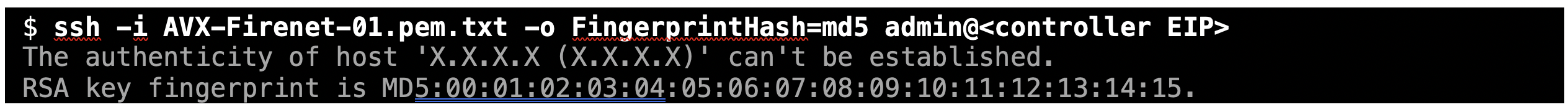
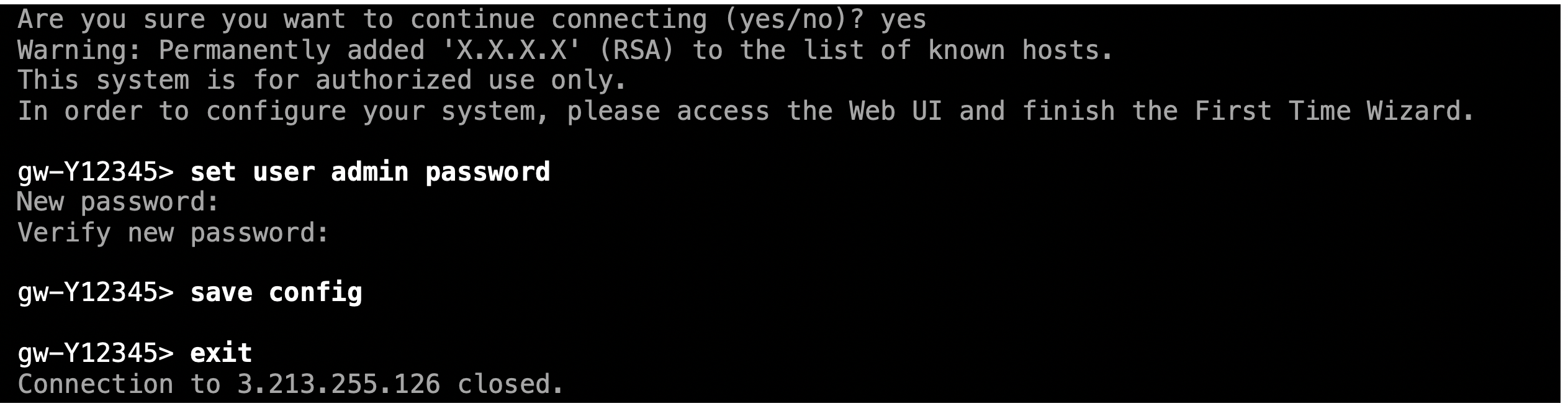
Now that the instance is up – open your preferred terminal and SSH into the instance using the proper keys and the user “admin”. It takes only two commands to set a new password.
Logging into the Gaia Portal
-
Please open a browser and go to https://management_eip/ to log into the Gaia Portal. You should be prompted with a screen like the one below. Just enter the user name as admin and the password you have just configured on the previous step.
-
Go to Network Management > Network Interfaces. You should simply double-check whether all interfaces are active and with a valid IP address;
Updating the Route Table
-
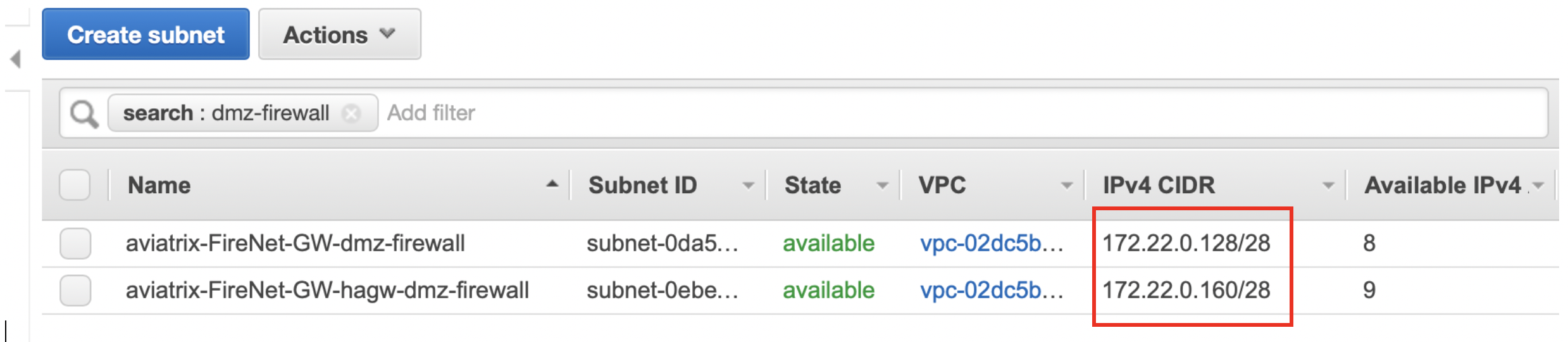
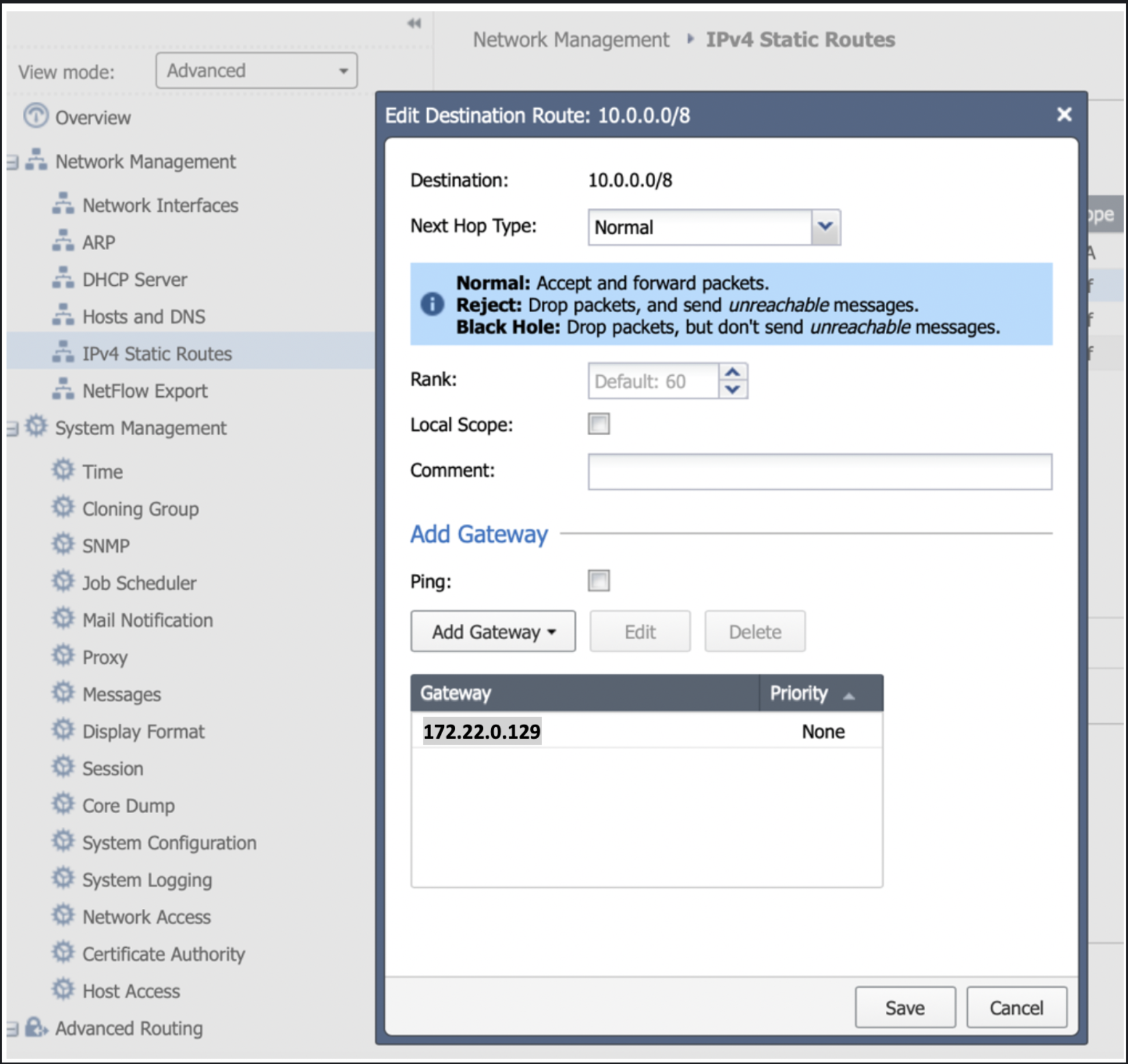
The next step is to update the route table. For the purpose of this guide, we suggest adding three return routes, each for a RFC1918 address pointing back to the VPC router of the subnet aviatrix*dmz-firewall (or aviatrix*hagw-dmz-firewall if you are attaching the instance to the backup gateway instead). Please go to the AWS console > VPC > Subnets and filter by “dmz-firewall” – that will allow you to determine the VPC router IP, which is the first host of each subnet.
-
Once you have determined the IP of the next hop, just go to IPv4 Static Routes and click on “Add”. Repeat this step for all three RF1918 subnets.
Downloading and Installing the SmartConsole
-
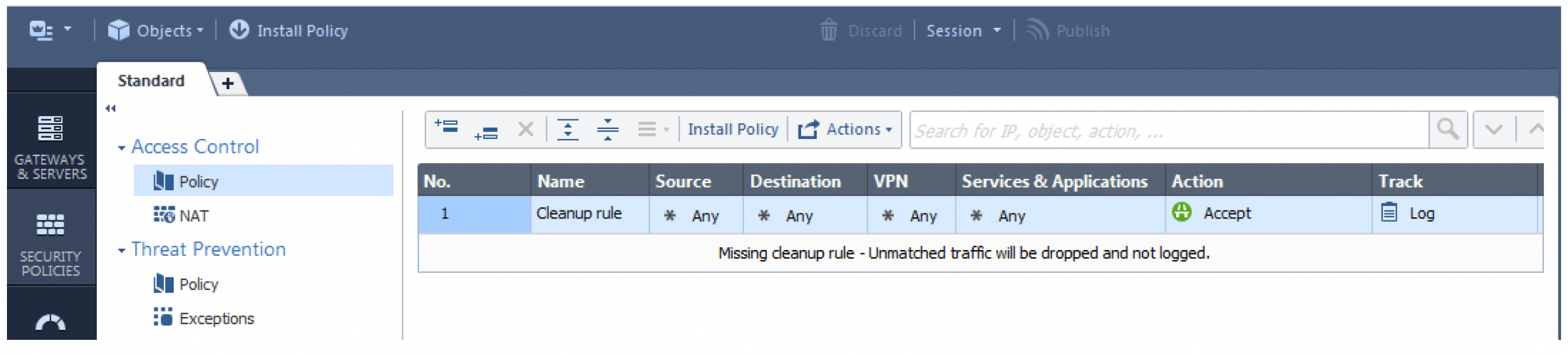
Download and install the SmartConsole if you have not done so already using this link: R80.10. On SmartConsole you need to define a security policy that will allow the traffic to be inspected/logged and update the topology.
-
In the SmartConsole go to via Security Policies and then Policy and change the default policy to ‘accept’ traffic and to ‘Log’ it as well. This can (and SHOULD) be customized to comply with your project requirements. Finally, install the policy on the gateway(s) in question. Your basic policy should look like this
-
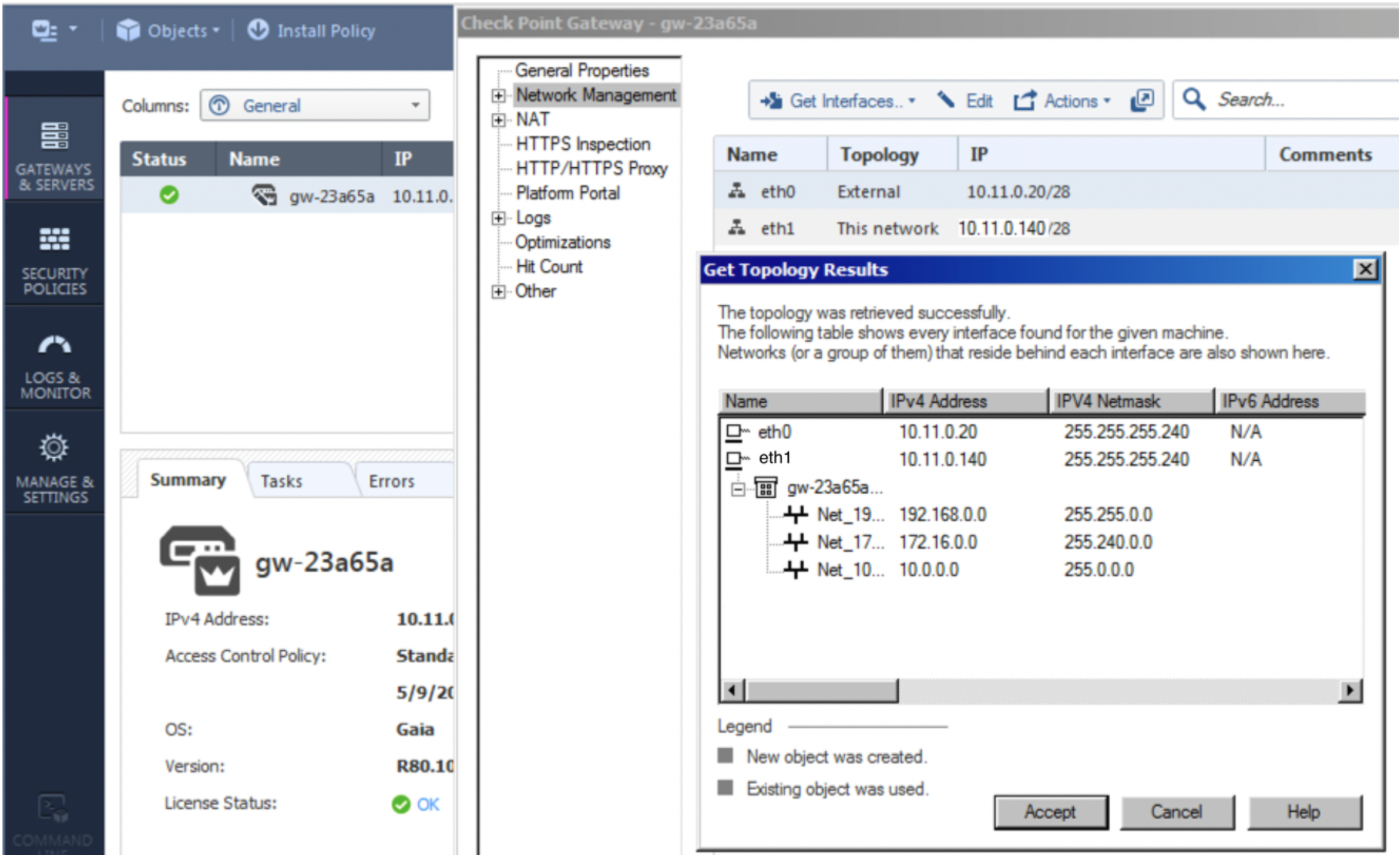
As per the topology page, it can be reached via Gateways & Servers and a double-click on the gateway itself. Then click on Network Management > Get Interfaces.
-
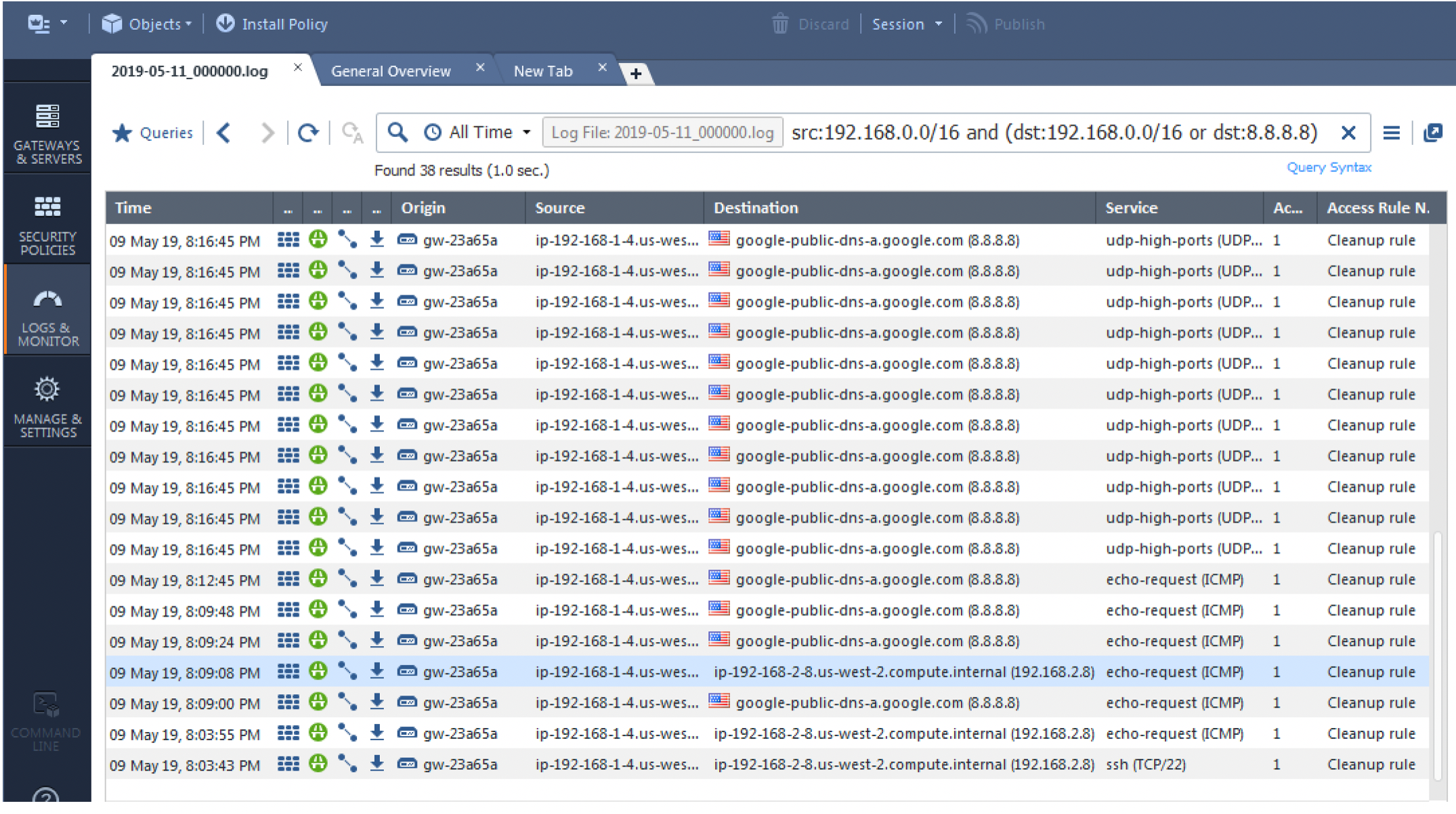
The final step is to monitor your traffic to confirm that the inspection is being performed as configured. Go to Logs & Monitor.
You can repeat this process to attach another CloudGuard instance to the backup Aviatrix gateway. The difference regarding the backup gateway attachment is that the subnets should be in a different AZ.