Configuring Palo Alto in OCI
Example Config for Palo Alto Network VM-Series in OCI
In this document, we provide an example to set up the VM-Series for you to validate that packets are indeed sent to the VM-Series for VCN to VCN and from VCN to internet traffic inspection.
VM-Series in AWS can be set up using Palo Alto Networks VM-Series AWS Example.
VM-Series in Azure can be set up using the guide Palo Alto Networks VM-Series Azure Example.
The Aviatrix Firewall Network (FireNet) workflow launches a VM-Series at this step. After the launch is complete, the console displays the VM-Series instance with its public IP address of management interface and allows you to download the .pem file for SSH access to the instance.
Below are the steps for the initial setup.
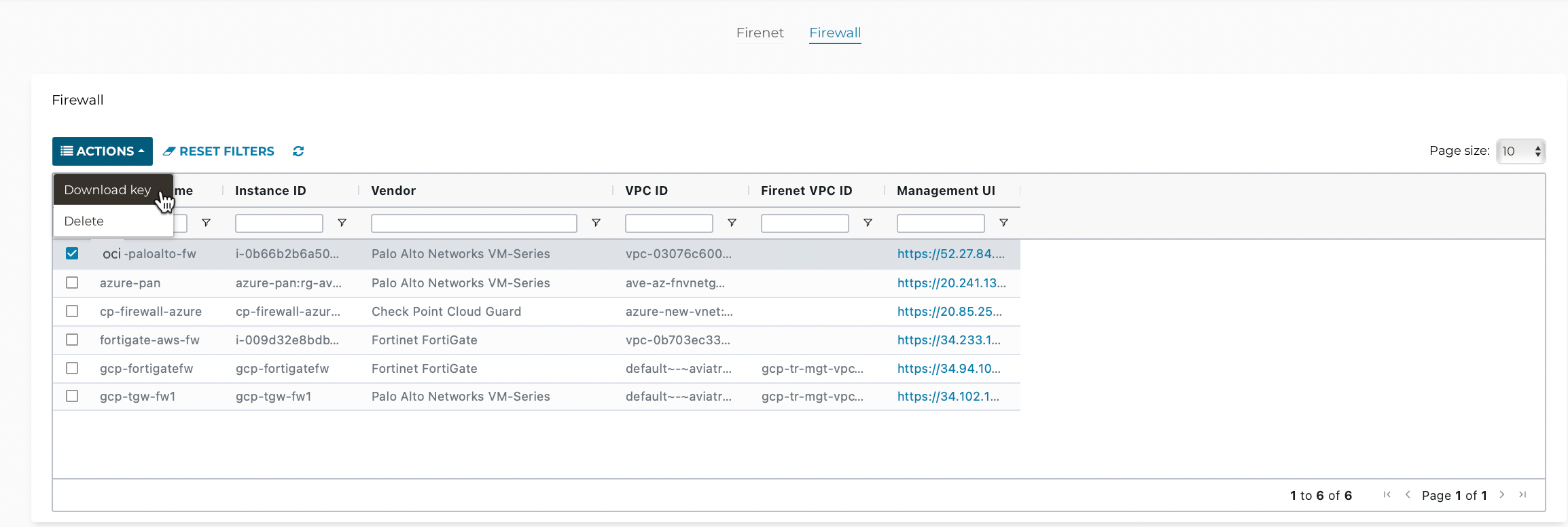
Downloading VM-Series Access Key
After launching and associating a firewall instance, navigate to Firewall Network > List > Firewall, select the firewall instance, and then click Actions > Download key.
If you get a download error, usually it means the VM-Series is not ready. Wait until it is ready, refresh the browser and then try again.
Resetting VM-Series Password
| After you download the .pem file, change the file permission to 600. If you are asked to enter a password during the login, the VM-Series is still not ready. Wait and try again. It usually takes up to 15 minutes for the VM-Series to be ready. When the VM-Series is ready, you will no longer be prompted for a password. |
For Metered AMI, open a terminal and run the following command.
ssh -i <private_key.pem> admin@<public-ip_address> configure set mgt-config users admin password commit
For BYOL, open a terminal and run the following command.
ssh -i <private_key.pem> admin@<public-ip_address> configure set mgt-config users admin password set deviceconfig system dns-setting servers primary <ip_address> commit
Terminate the SSH session.
Logging in to VM-Series
-
In the Aviatrix Controller, navigate to Firewall Network > List > Firewall.
-
Select a firewall and click on the Management UI link. It takes you to the VM-Series you just launched.
-
Login with Username "admin." The password is the password you set in the previous step.
Dynamic Updates
-
From Device > Dynamic Updates, click on Check Now to download and then install the latest versions of Applications and Threats and Wildfire updates.
-
Click on Check Now again to download and then install the latest version of Antivirus.
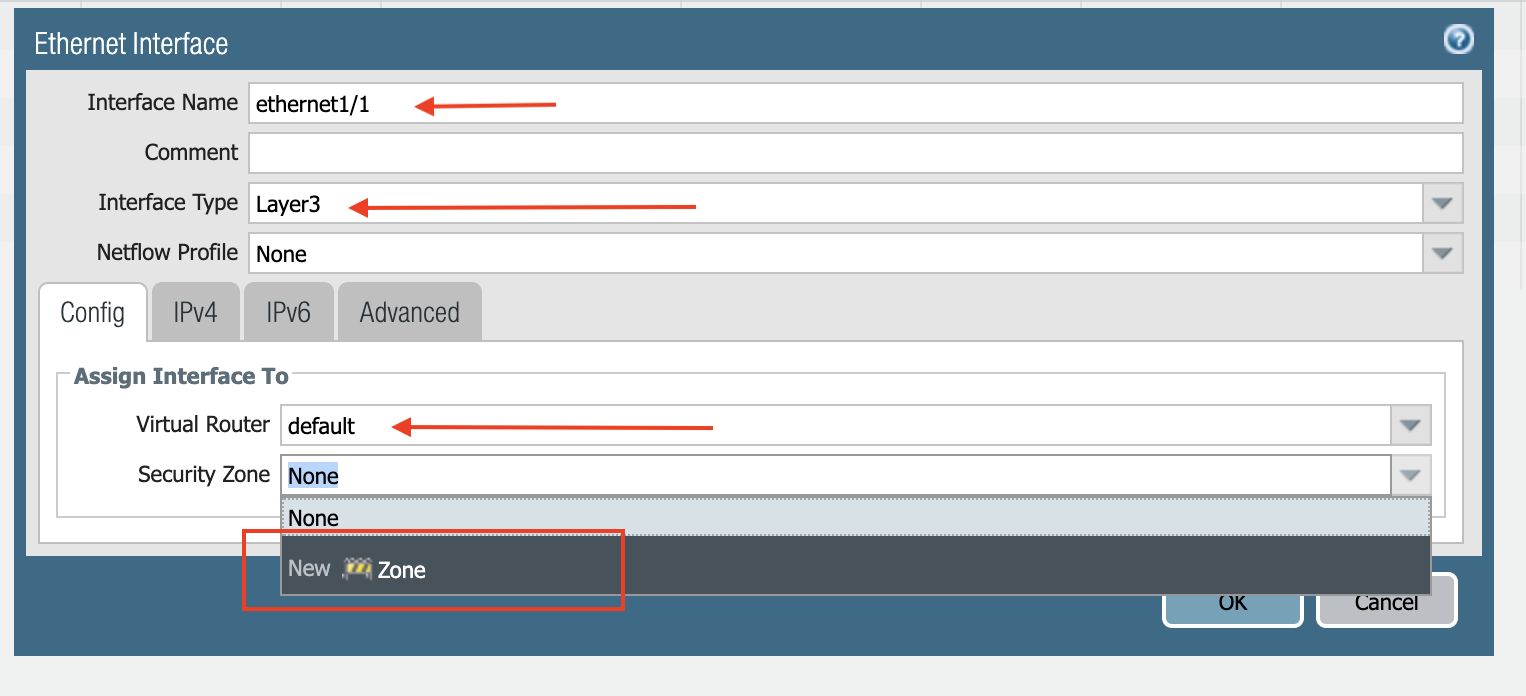
Configuring VM-Series ethernet1/1 with WAN Zone
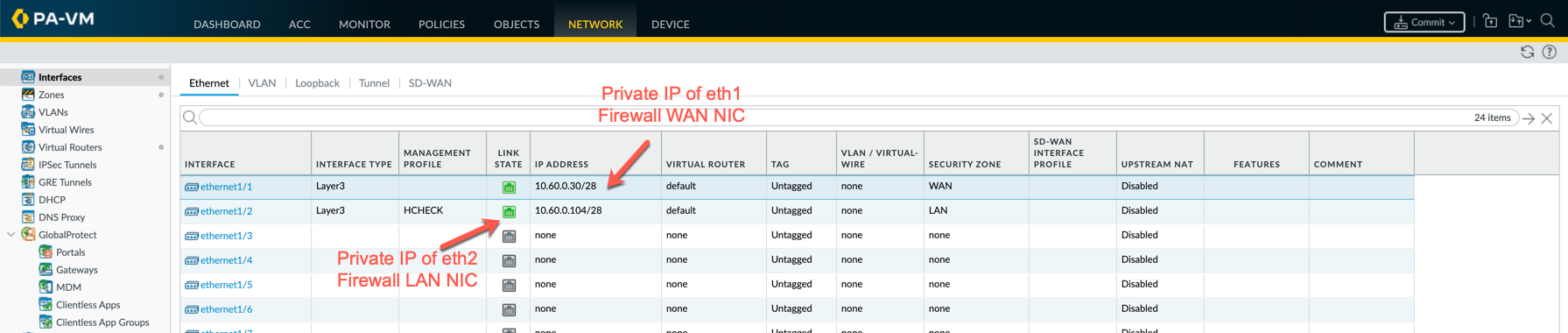
After logging in, select the Network tab to see a list of ethernet interfaces. Click ethernet1/1 and configure as per the following screenshot.
-
Select the Network tab.
-
Click ethernet1/1.
-
Select "layer3" for Interface Type.
-
Select the Config tab in the popup Ethernet Interface window.
-
Select the default for Virtual Router at Config tab.
-
Click New Zone for Security Zone to create a WAN zone.
-
At the next popup screen, name the new zone "WAN" and click OK.
-
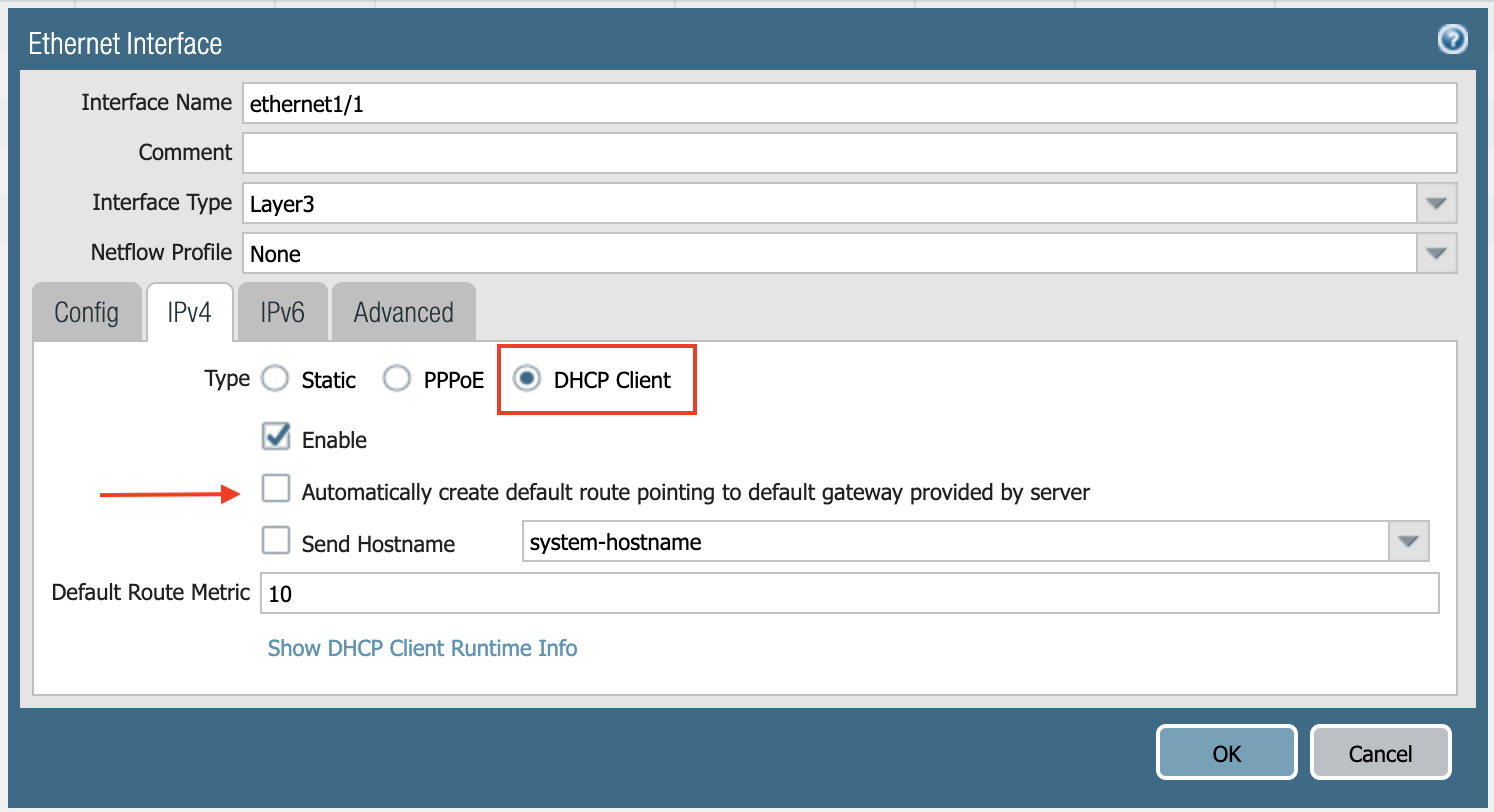
Select the IPV4 tab in the popup Ethernet Interface window.
-
Select Static.
-
Add the Private IP of eth1 firewall WAN NIC, as shown below.
-
Click Commit. Once Commit is complete, you should see the Link State turn green at the Network page for ethernet1/1.
Configuring VM-Series ethernet1/2 with LAN Zone
Repeat the steps in the Configuring VM-Series ethernet1/1 with WAN Zone section above for ethernet1/2. Name the new zone LAN. Also, allow ICMP on LAN interface for health check, as shown below.
-
Go to Network > Interface Mgmt under Network Profiles and click Add.
-
Give any name in Interface Management Profile, check Ping or ICMP checkbox under Administrative Management Service, and click OK.
-
Attach Profile with LAN interface: go to Network > Interfaces > Select LAN Ethernet Interface > Advanced > Management Profile > Select the appropriate profile.
-
Click Commit. Once Commit is complete, you should see the Link State turn green at the Network page for ethernet1/2.
Configuring Allow All Policies
Go to Policies > Security. Click Add.
-
Name the policy > Allow-All.
-
Source tab > Any.
-
Destination tab > Any.
-
Application tab > Any.
-
Click OK.
Configuring NAT for Egress
If you would also like to enable NAT to test egress, follow these steps.
-
Navigate to Policies > NAT and click Add.
-
Select the General tab and name the policy.
-
Click Original Packet.
-
At Source Zone, click Add and select LAN.
-
At Destination Zone, select WAN.
-
At Destination Interface, select Ethernet1/1, as shown below.
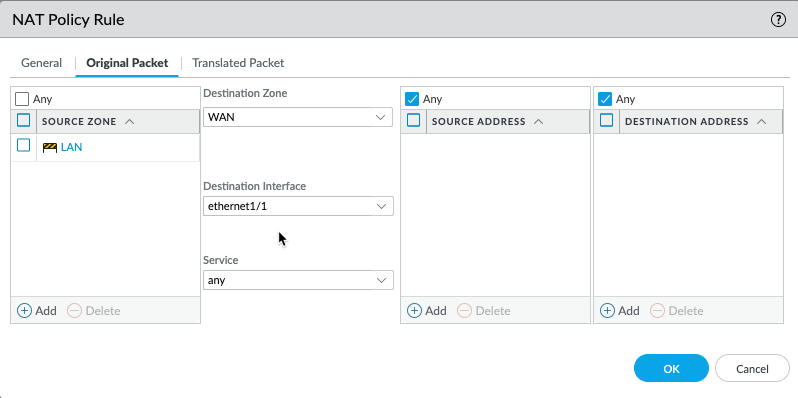
-
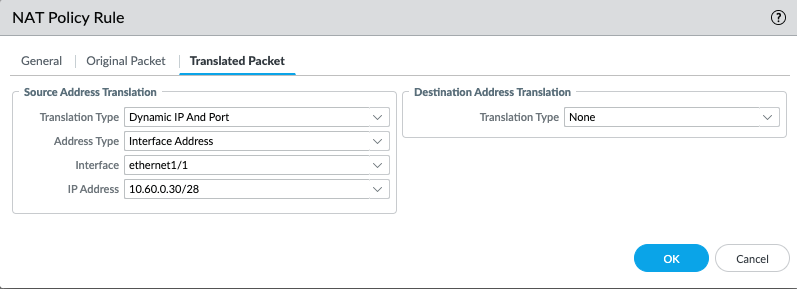
Click Translated Packet.
-
At Translation Type, select Dynamic IP And Port.
-
At Address Type, select Interface Address.
-
At Interface, select ethernet1/1, as shown below.
Setting up API Access
For the Aviatrix Controller to automatically update firewall instance route tables, monitor firewall instance health, and manage instance failover, you need to set up API access permissions.
Follow the instructions here to enable API access.