Aviatrix Gateway to Check Point (R80.10)
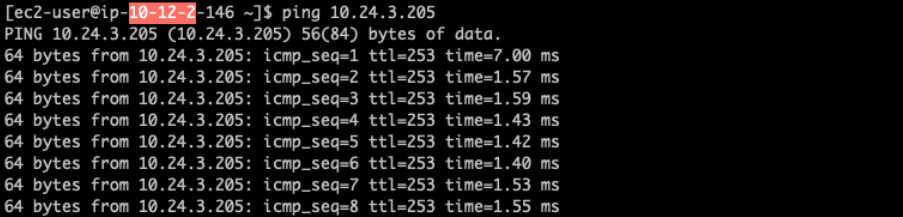
This document describes how to build an IPsec tunnel based Site2Cloud connection between Aviatrix Gateway and Check Point Firewall. To simulate an on-prem Check Point Firewall, we use a Check Point CloudGuard IaaS firewall VM at AWS VPC.
|
If you do not have access to AWS, you can simulate an on-prem Firewall by deploying the Palo Alto Firewall in any other cloud (such as Microsoft Azure, Google Cloud Platform, or Oracle Cloud Infrastructure). |
The network setup is as follows:
VPC1 (with Aviatrix Gateway)
VPC1 CIDR: 10.12.0.0/16
VPC1 Public Subnet CIDR: 10.12.0.0/23
VPC1 Private Subnet CIDR: 10.12.2.0/23
VPC2 (with Check Point Security Gateway)
VPC2 CIDR: 10.24.0.0/16
VPC2 Public Subnet CIDR: 10.24.0.0/23
VPC2 Private Subnet CIDR: 10.24.2.0/23
Launching Check Point Security Gateway VM
Launch a CheckPoint VM with at least two network interfaces. One interface serves as a WAN port and is in VPC2’s public subnet. The other interface serves as a LAN port and is in VPC2’s private subnet. Collect the public IP address of the WAN port.
Creating an External Connection
-
In Aviatrix CoPilot, launch an Aviatrix Transit Gateway in VPC1’s public subnet. Collect both the public and private IP address of the Gateway.
-
Navigate to Networking > Connectivity > External Connections (S2C) and click Add New to create a Site2Cloud connection (selecting Pre-Shared Key) using the values for one of the below options:
-
Substitute the following values:
-
Remote Gateway Type: Generic
-
Algorithms: turn Off
-
Remote Gateway IP: Public IP of the Check Point VM WAN port
-
Remote Subnet CIDR(s): 10.24.2.0/23 (VPC2 private subnet)
-
Local Subnet CIDR(s): 10.12.2.0/23 (VPC1 private subnet)
-
-
After the connection is created, select the vertical ellipsis
 menu for that connection and select Download Configuration.
menu for that connection and select Download Configuration. -
Select Generic from the Vendor dropdown list and click the Download to download the external (S2C) configuration. Use this configuration file to configure the tunnels and interfaces in your Check Point VM firewall.
Downloading and Installing SmartConsole
-
Using a browser, connect to the Gaia Portal of the CheckPoint-VM at https:/CheckPoint-VM_Public-IP:
-
Click Download Now! as shown below to download SmartConsole.
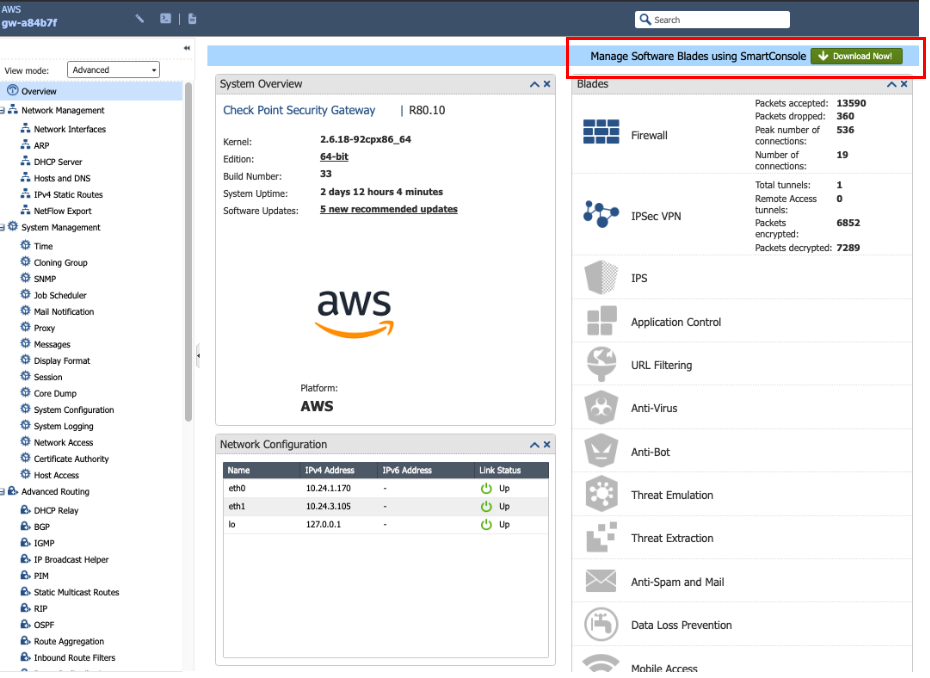
-
Install SmartConsole at your local machine and launch SmartDashboard.
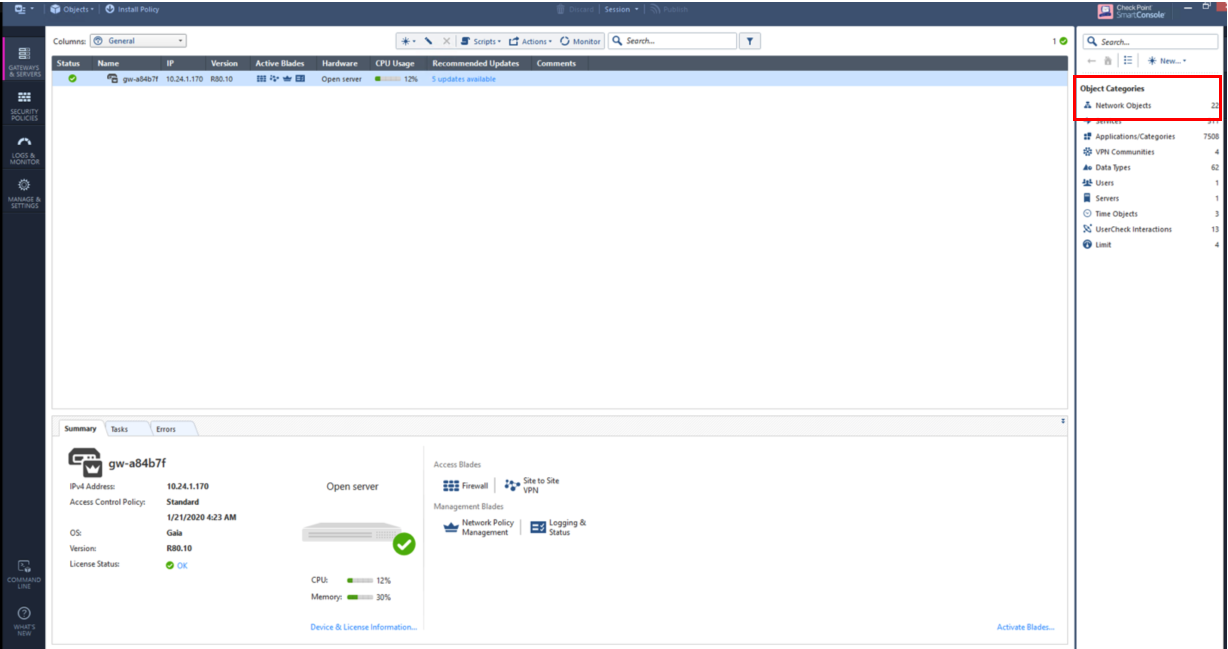
Creating Network Objects at SmartConsole
-
At the Check Point SmartDashboard window, go to New > Network and create two objects.
-
Create one network for private subnet of VPC2 (Check Point VPC).
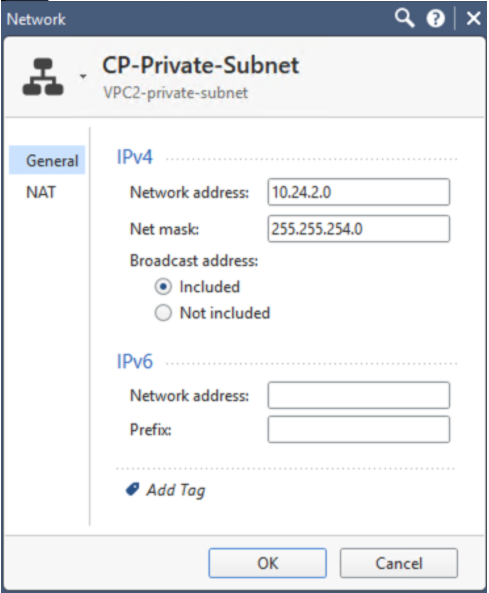
Field Value Name
Arbitrary (e.g. CP-Private-Subnet)
IPv4 Network Address
VPC2 private subnet CIDR
IPv4 Net mask
VPC2 private subnet mask
-
Create one network for private subnet of VPC1 (Aviatrix Gateway VPC).
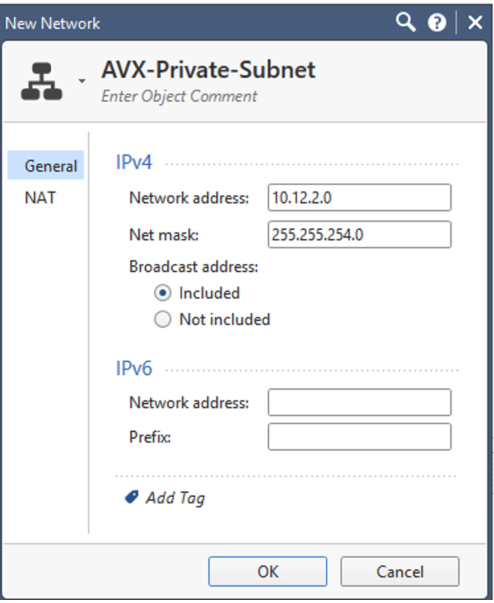
Field Value Name
Arbitrary (e.g. AVX-Private-Subnet)
IPv4 Network Address
VPC1 private subnet CIDR
IPv4 Net mask
VPC1 private subnet mask
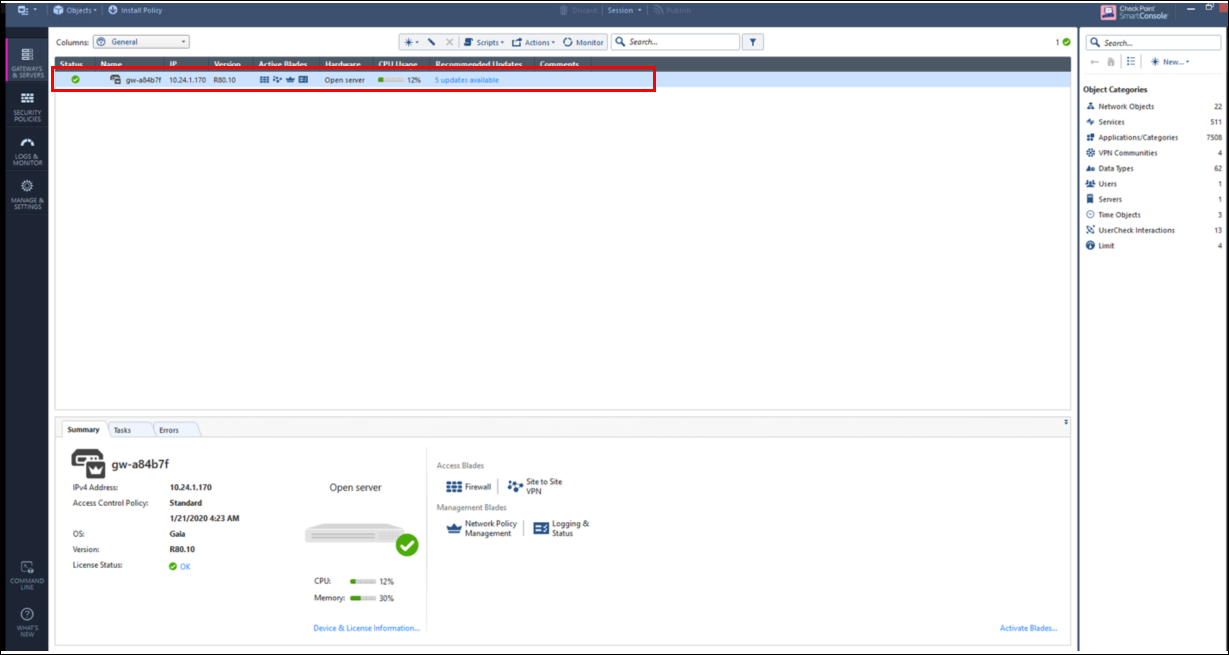
Configuring Check Point Security Gateway with VPN
-
At the SmartDashboard window, go to Gateways and services > double-click on the gateway.
-
Enter the private IP of the Check Point VM WAN port in the IPv4 address field.
-
Under Network Security, select IPsec VPN.
-
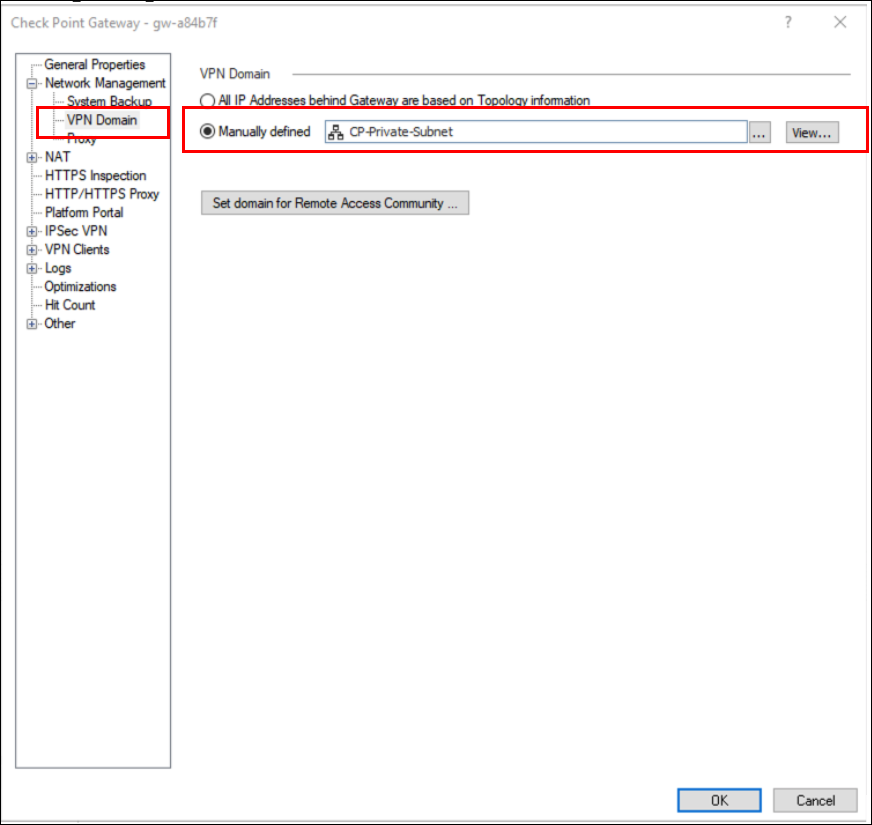
Go to Network management > VPN domain > click Manually defined and select the network created previously (see Creating Network Objects at SmartConsole above).
-
Go to Network management and double-click "eth0" (Check Point WAN port).
-
Select External (leads out to the Internet) and click OK.
-
Go to Network management and double-click "eth1" (Check Point LAN port).
-
Click on modify.
-
Select the following:
-
Override
-
This network (internal)
-
Specific, and select the network created previously (see Creating Network Objects at SmartConsole above).
-
-
Click OK.
-
Double-click on gateway as shown in step 1 above.
-
Select IPsec VPN in the left menu and then select the Statically NATed IP radio button.
-
Next to this radio button, enter the public IP of the Check Point WAN port.
-
Double-click on the gateway as shown in step 1 above.
-
Select VPN Advanced in the left menu and ensure that Use the community settings is selected.
-
Ensure that the Support NAT traversal checkbox is selected.
-
Click OK.
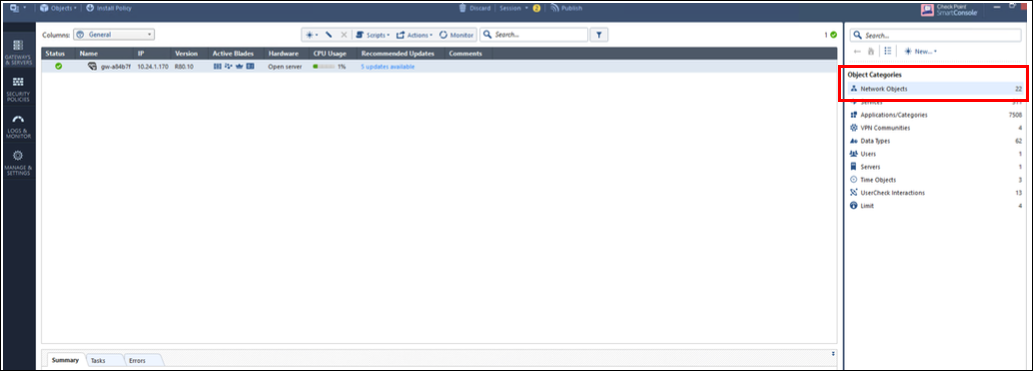
Configuring an Interoperable Device to Represent Aviatrix Gateway
-
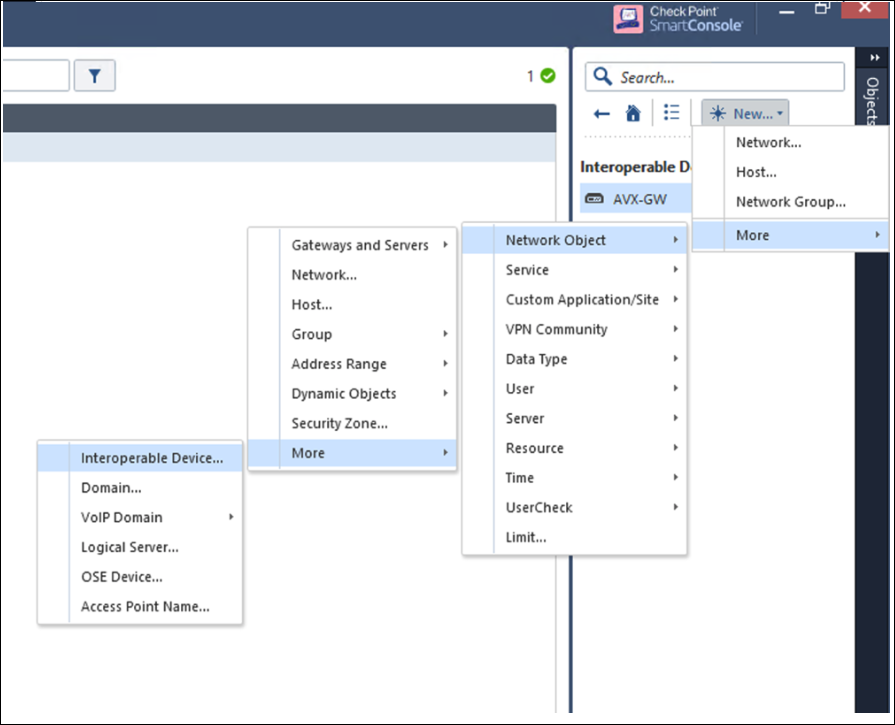
Go to Gateways and services > New network objects > Interoperable devices.
-
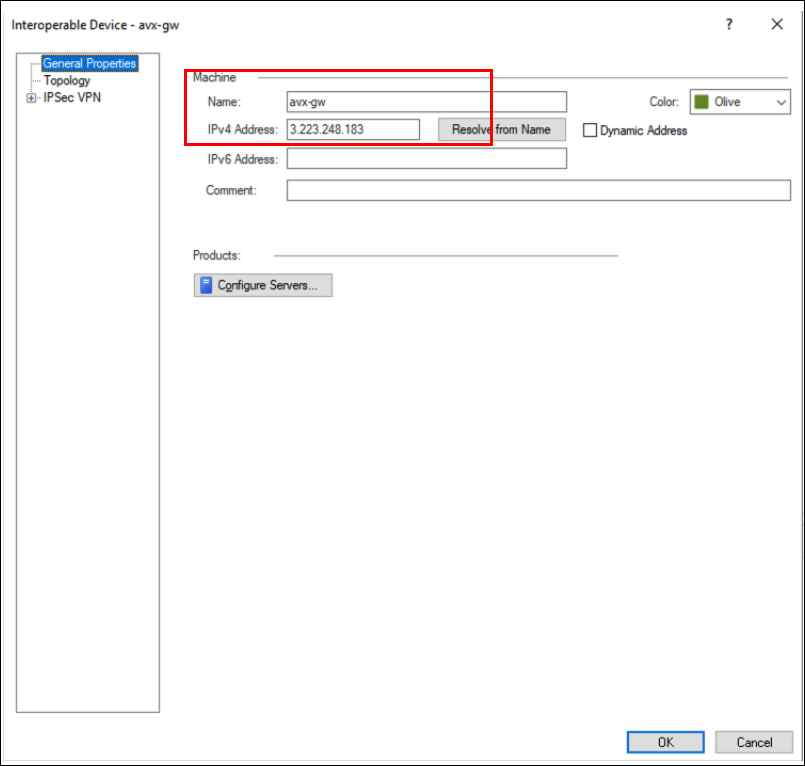
Click Add new and then use the image below to create a new interoperable device to represent Aviatrix Gateway.
-
Double-click on Interoperable device > avx-gwv (created in step 1 of this section) > General properties. The IPv4 address will be the public IP of the Aviatrix Gateway.
-
Double-click on Interoperable device > avx-gwv (created in step 1 in this section).
-
Select Topology in the left menu and select the Manually defined radio button.
-
In the field next to the radio button, select the network for the private subnet of the VPC1 (Aviatrix Gateway VPC) network created above.
-
Click OK.
-
Double-click on Interoperable device > avx-gwv (created in step 1 of this section.
-
Click Link Selection under IPsec VPN in the left menu and then select the Always use this IP address and Main address radio buttons.
-
Click OK.
-
Double-click on Interoperable device > avx-gwv (created in step 1 of this section).
-
Select VPN Advanced under IPsec VPN in the left menu.
-
Select Use the community settings and click OK.
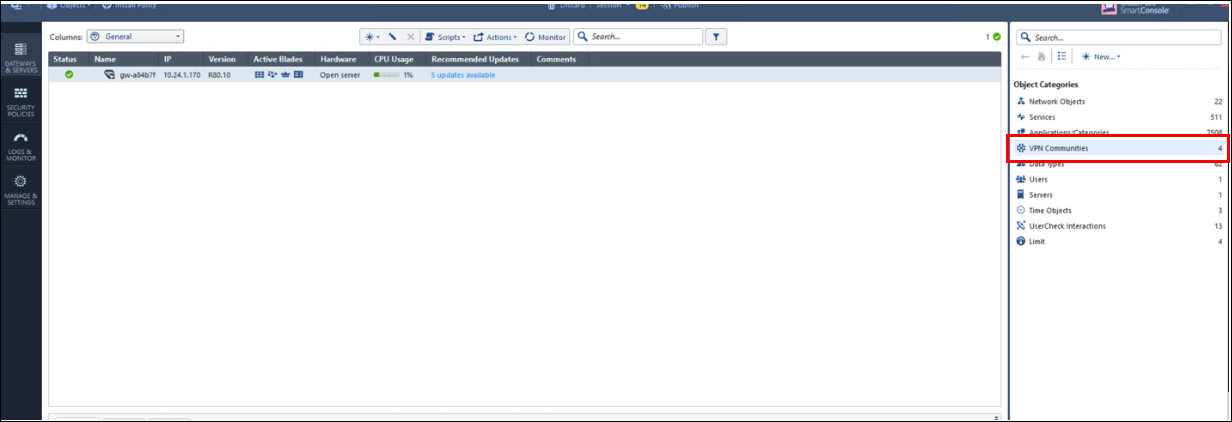
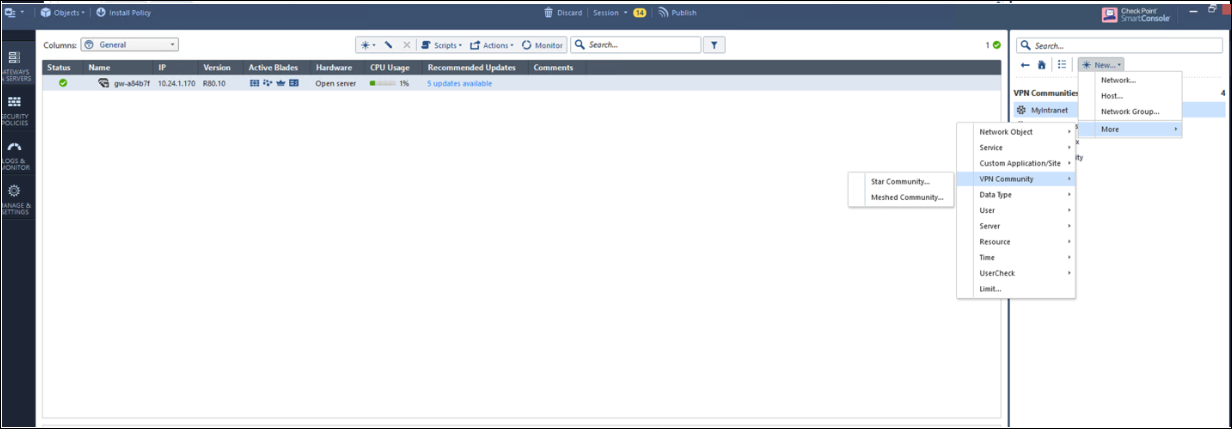
Creating a VPN Community
-
Click on VPN communities on the smart console. Then, create a Star Community as shown below.
-
After creating the VPN community, double-click on the created VPN community > Gateway tab.
-
In the star-community dialog, select the gateway created above (see Configuring Check Point Security Gateway with VPN).
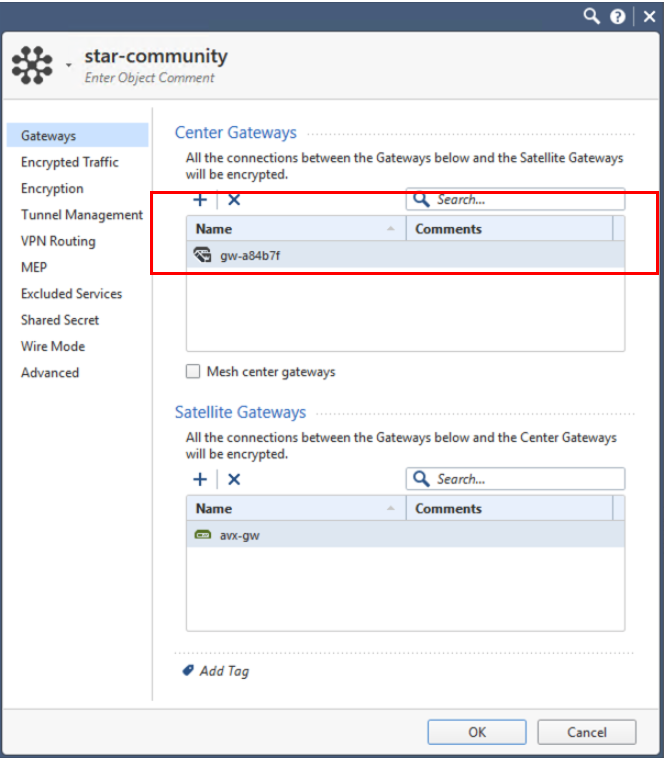
-
Click OK.
-
Double-click on the created VPN community and then select Encryption in the left menu.
-
Select the options according to the Site2Cloud configuration downloaded previously (see Creating an External Connection above).
-
Click OK.
-
Double-click on the created VPN community and then select Tunnel management in the left menu.
-
Select Set Permanent Tunnels / On all tunnels in the community.
-
Select the One VPN tunnel per Gateway pair radio button.
-
Click OK.
-
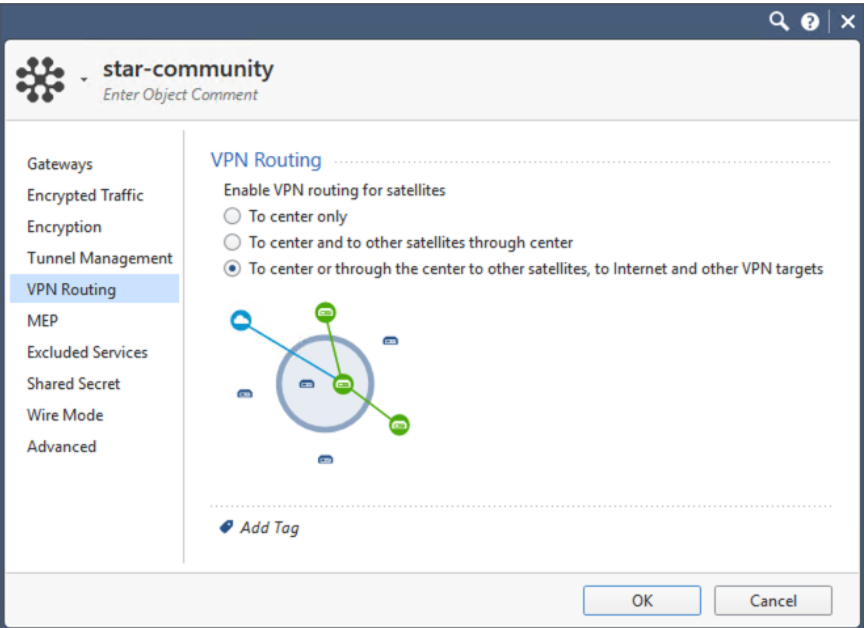
Double-click on created VPN community > VPN routing > select as shown in the image below.
-
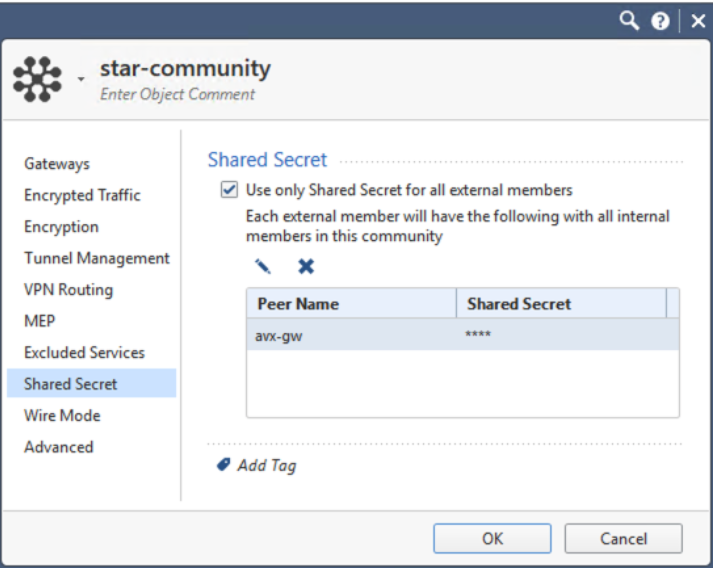
Double-click on the created VPN community. In the left menu select Shared Secret.
-
Enter the Shared Secret by copying the Pre-Shared Key from the Site2Cloud configuration downloaded previously (see Creating an External Connection above).
-
Click OK.
-
Double-click on the created VPN community.
-
In the left menu select Advanced.
-
Enter the Phase1 and Phase2 parameters according to the Site2Cloud configuration downloaded previously (see Creating an External Connection above).
-
Click OK.
Creating Firewall Rule for VPN Traffic
-
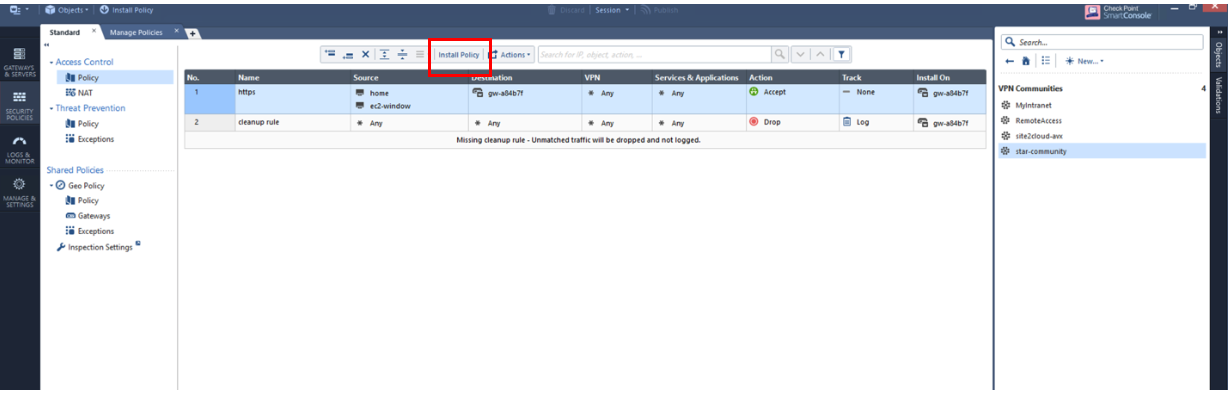
Go to security and policies. Add a policy and click Install Policy.
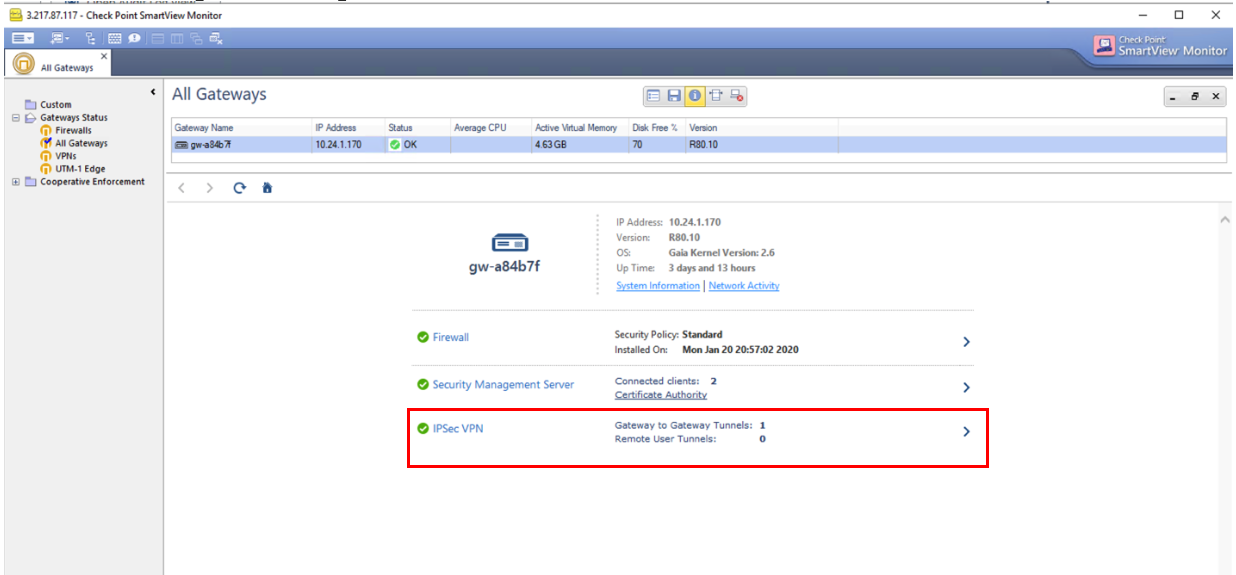
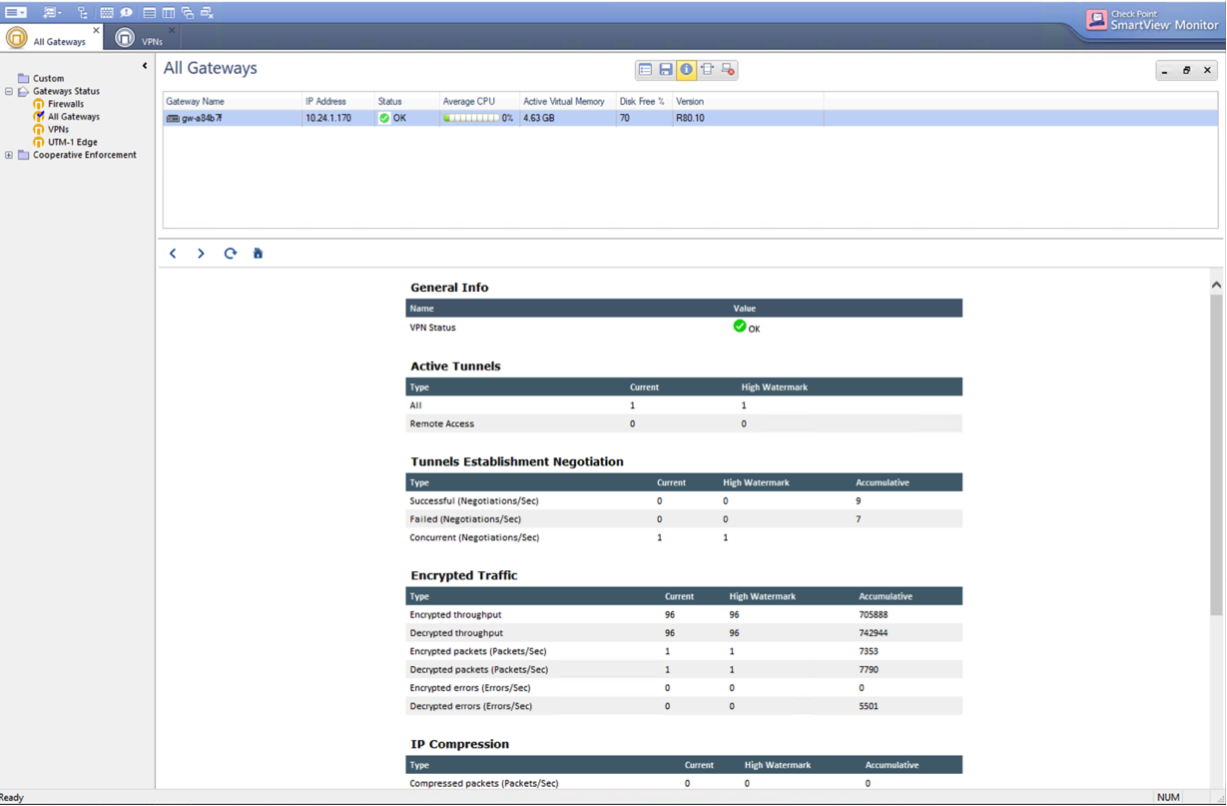
Troubleshooting and Verifying at Check Point Security Gateway
-
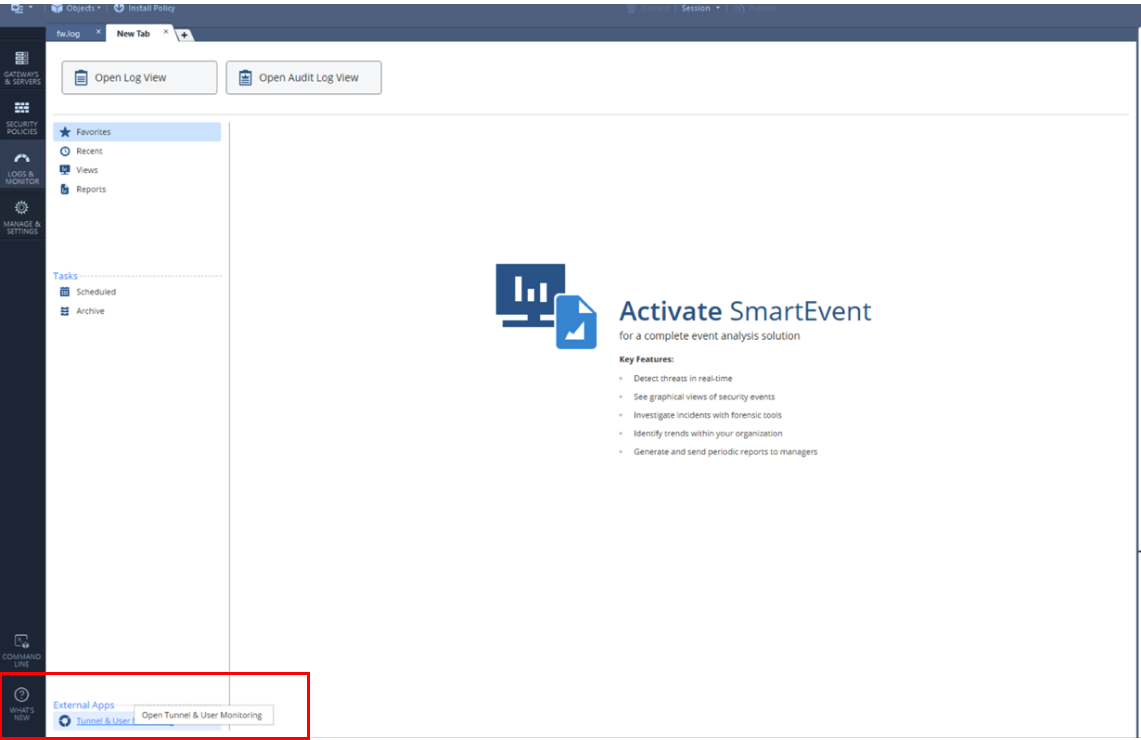
Go to Logs and monitor and dd a new tab.
-
Click Open Tunnel & User Monitoring.
-
Click IPsec VPN to see the tunnel status.