GRE Tunneling for Multicloud Transit Gateway to On-Prem
Introduction
Connecting to on-prem network over GRE tunneling protocol in AWS is an alternative to IPsec. When GRE tunneling is used, Aviatrix Multicloud Transit Gateways interoperate directly with on-prem network devices over AWS Direct Connect.
When on-prem to cloud encryption is not required, using GRE allows you to achieve high performance throughput (10Gbps) without the need to deploy Aviatrix CloudN appliance.
The solution is shown in the diagram below,
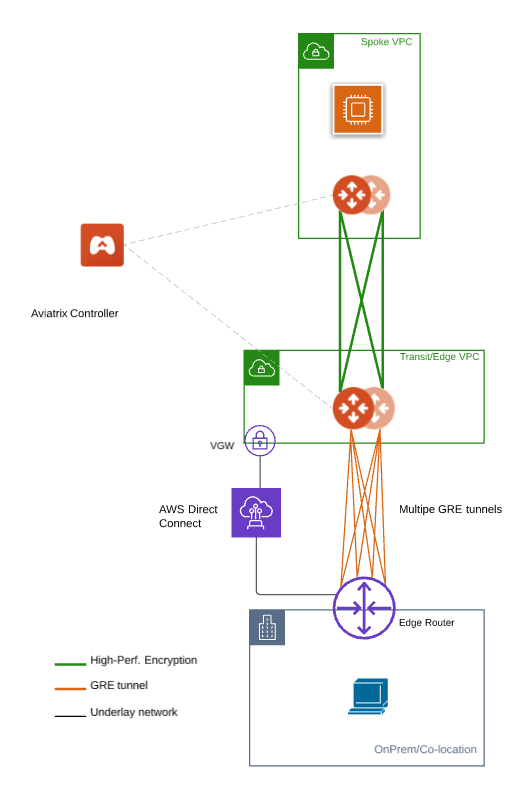
where Aviatrix Multicloud Transit Gateways connect to an on-prem edge router over Direct Connect.
This document gives step-by-step instructions on how to build Aviatrix Transit Gateway to External Device using GRE over AWS Direct Connect. In this Tech Note, you learn the following:
-
Workflow on building underlay connectivity with AWS Direct Connect 10 Gbps capacity
-
Workflow on deploying Aviatrix Transit Solution
-
Workflow on establishing connectivity between edge router and Aviatrix Transit Gateway to form GRE tunnel
-
Workflow on building GRE tunnel and BGP over GRE
-
Workflow on enabling ECMP Load Balancing to achieve high performance
For more information about Multicloud Transit Network and External Device, please see these documents:
|
The key ideas for this solution are:
-
The edge (WAN) router runs a BGP session to AWS VGW via AWS Direct
Connect where the edge router advertises its GRE IPs. AWS VGW advertises the AWS Transit VPC CIDR. * Leverage edge router BGP ECMP feature. * Configure multiple GRE tunnels for greater aggregate throughput.
|
Prerequisite
-
Upgrade Aviatrix Controller to the latest version.
-
In this example, we are going to deploy the below VPCs in AWS:
-
AWS Aviatrix Transit VPC (i.e. 10.1.0.0/16) by utilizing Aviatrix feature Create a VPC with Aviatrix FireNet VPC option enabled
-
AWS Aviatrix Spoke VPC (i.e. 192.168.1.0/24) by utilizing Aviatrix feature Create a VPC as the previous step or manually deploying it in each cloud portal. Moreover, feel free to use your existing cloud network.
-
-
Edge router has high throughput supported on hardware interface(s) and GRE tunnel(s)
Building Underlay Connectivity with AWS Direct Connect
Building AWS Direct Connect is customer’s responsibility. For more information about AWS Direct Connect, please see Connect Your Data Center to AWS.
Please adjust the topology depending on your requirements.
Building AWS Direct Connect
See Equinix ECX Fabric AWS Direct Connect if users select Equinix solution. This is just an example here. Make sure to select 10 Gbps capacity.
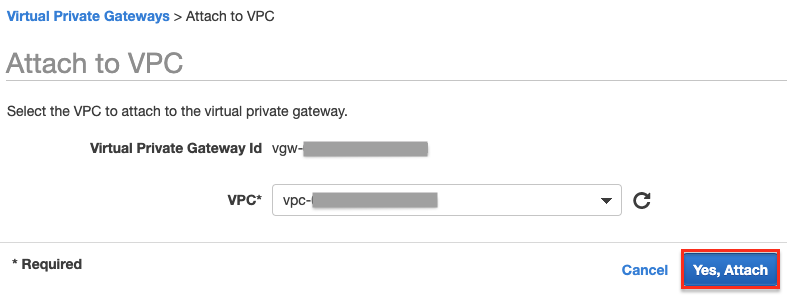
Associating AWS VGW to AWS Transit VPC
-
Log in to the AWS VPC Portal and select Virtual Private Gateways under the Virtual Private Network (VPN) sidebar.
-
Select the Virtual Private Gateway that you have the private virtual interface to AWS Direct Connect
-
Click Actions.
-
Select Attach to VPC.
-
Select the AWS Transit VPC and click Yes, Attach.
Deploying the Aviatrix Multicloud Transit Solution
Refer to Global Transit Network Workflow Instructions for the steps below. Please adjust the topology depending on your requirements.
Step 2.1. Deploy Aviatrix Multicloud Transit Gateway and HA in AWS
-
Follow this step Deploy the Aviatrix Transit Gateway to launch Aviatrix Transit gateway and enable HA with insane mode enabled in AWS Transit VPC
-
In this example, sizes c5n.2xlarge and c5n.4xlarge are selected to benchmark performance.
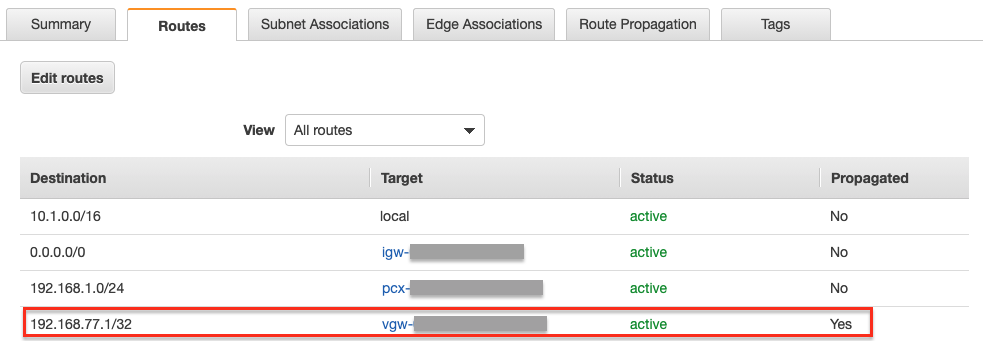
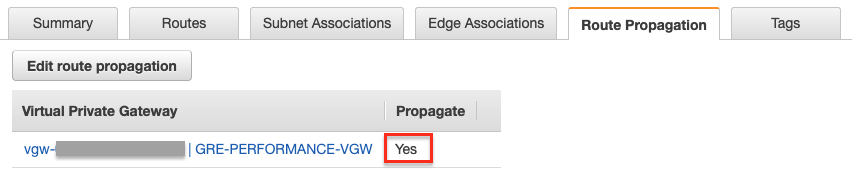
Enabling Route Propagation on the Subnet Route Table where Aviatrix Transit Gateway Locates on AWS Portal
-
Log in to the AWS VPC portal and locate the subnet route table where Aviatrix Transit Gateway is located.
-
Select Route Propagation tab.
-
Click Edit route propagation.
-
Locate the AWS VGW that is associated with this Transit VPC and mark the Propagate checkbox.
-
Click Save.
-
Check whether the Propagate status is Yes.
Deploying Spoke Gateway and HA
Follow this step Deploy Spoke Gateways to launch Aviatrix Spoke gateway and enable HA with insane mode enabled in AWS Spoke VPC.
In this example, sizes c5n.2xlarge and c5n.4xlarge are selected to benchmark performance.
Attaching Spoke Gateways to Transit Network
Follow this step Attach Spoke Gateways to Transit Network to attach Aviatrix Spoke Gateways to Aviatrix Transit Gateways in AWS.
Building Connectivity between Edge Router and Aviatrix Transit Gateway
Cisco ASR is used as an edge router in this example.
Checking Whether the edge router has Learned AWS Transit VPC CIDR via the BGP Session Between Edge Router and AWS Direct Connect
-
Log in to the edge router (i.e. Cisco ASR)
-
Check whether edge router has learned AWS Transit VPC CIDR via the BGP session between edge router and AWS Direct Connect by issuing the related "show ip bgp" command
Simple Cisco IOS example:
#show ip bgp
Preparing IP for GRE source IP on Edge Router
In this example, we use ASR loopback interface with an unique IP address as a GRE source IP.
Create a loopback interface and assign an IP to itself as a GRE source IP.
Simple Cisco IOS example:
#configure t (config)#interface Loopback77 (config-if)#ip address 192.168.77.1 255.255.255.255
Advertising that GRE source IP on Edge Router to the BGP Session Between Edge Router and AWS Direct Connect
The purpose of this step is to let AWS VGW learn the GRE source IP on edge router via BGP session between edge router and AWS Direct Connect,
so that Aviatrix Transit Gateway can reach the GRE source IP on edge router to form GRE tunnel over AWS Direct Connect.
To demonstrate this concept in a simple fashion, we utilize IOS "ip prefix-list" function and apply it on BGP neighbor with direction out function to distribute GRE source IP.
Create a prefix list that defines GRE source IP on edge router for BGP advertisement.
Simple Cisco IOS example:
#configure t (config)#ip prefix-list Router-to-VGW description Advertised GRE source CIDRs 192.168.77.X/32 to build GRE tunnels (config)#ip prefix-list Router-to-VGW seq 10 permit 192.168.77.1/32
Apply this prefix list to outgoing BGP advertisements
Simple Cisco IOS example:
#configure t (config)#router bgp 65000 (config-router)#address-family ipv4 (config-router-af)#neighbor 169.254.253.17 prefix-list Router-to-VGW out
Notes:
The IP 169.254.253.17 in this example here is the AWS Direct Connect BGP Peer IP.
Build GRE tunnel and BGP over GRE
Configuring GRE tunnel and BGP on Aviatrix Transit Gateway
-
Log in to your Aviatrix Controller and navigate to Multi-Cloud Transit > Setup > External Device tab.
-
Select option External Device > BGP > GRE.
-
Use the fields below to set up GRE tunnel to edge router.
Transit VPC Name |
Select the Transit VPC ID where Transit GW was launched. |
Connection Name |
Provide a unique name to identify the connection to external device. |
Aviatrix Transit Gateway BGP ASN |
Configure a BGP AS number that the Transit GW will use to exchange routes with external device. |
Primary Aviatrix Transit Gateway |
Select the Transit GW. |
Enable Remote Gateway HA |
Don’t check this option in this example. |
Over Private Network |
Check this option since AWS Direct Connect is underlay network |
Remote BGP AS Number |
Configure a BGP AS number that edge router will use to exchange routes with Transit GW |
Local Tunnel IP |
Leave it blank in this example. |
Remote Tunnel IP |
Leave it blank in this example. |
-
Click Connect to generate GRE tunnel and BGP session over it.
![][aviatrix_transit_externel_device_gre](_images/aviatrix-transit-externel-device-gre.png)
Downloading the GRE Configuration Sample from Aviatrix Controller
-
Navigate to Site2Cloud > Setup.
-
Select the connection that you created with �Connection Name? in the previous step
-
Click Edit.
-
Select Cisco as Vendor type, ISR, ASR or CSR as Platform, and IOS(XE) as Software for this example.
-
Click Download Configuration.
Configuring GRE tunnel on Edge Router
-
Open the downloaded GRE configuration file.
-
Populate these values as follows based on your setup throughout the Tunnel Interface Configuration.
-
<tunnel_number1>: the primary GRE tunnel interface number connecting Aviatrix Transit Primary Gateway (i.e. 11)
-
<tunnel_number2>: the secondary GRE tunnel interface number connecting Aviatrix Transit HA Gateway (i.e. 12)
-
<ios_wan_interface1>: the IP which is assigned on the Loopback interface as an GRE source IP (i.e. 192.168.77.1)
-
<ios_wan_interface2>: the IP which is assigned on the Loopback interface as an GRE source IP (i.e. 192.168.77.1)
-
-
Copy and paste the updated Tunnel Interface Configuration into edge router
Simple Cisco IOS example:
interface Tunnel 11 ip address 169.254.61.205 255.255.255.252 ip mtu 1436 ip tcp adjust-mss 1387 tunnel source 192.168.77.1 tunnel destination 10.1.0.185 ip virtual-reassembly no keepalive exit interface Tunnel 12 ip address 169.254.173.77 255.255.255.252 ip mtu 1436 ip tcp adjust-mss 1387 tunnel source 192.168.77.1 tunnel destination 10.1.1.27 ip virtual-reassembly no keepalive exit
Configuring BGP over GRE tunnel on Edge Router
-
Open the downloaded GRE configuration file and copy and paste the BGP Routing Configuration into edge router.
Simple Cisco IOS example:
router bgp 65000 bgp log-neighbor-changes neighbor 169.254.61.206 remote-as 65212 neighbor 169.254.61.206 timers 10 30 30 neighbor 169.254.173.78 remote-as 65212 neighbor 169.254.173.78 timers 10 30 30 ! address-family ipv4 redistribute connected neighbor 169.254.61.206 activate neighbor 169.254.61.206 soft-reconfiguration inbound neighbor 169.254.173.78 activate neighbor 169.254.173.78 soft-reconfiguration inbound maximum-paths 4 exit-address-family
-
Create a prefix list that defines CIDR where server locates in on-prem/co-location for BGP advertisement.
Simple Cisco IOS example:
#configure t (config)#ip prefix-list Router-To-Transit-GRE description Advertised on-prem CIDRs 10.220.5.0/24 (config)#ip prefix-list Router-To-Transit-GRE seq 10 permit 10.220.5.0/24
-
Apply the prefix list to outgoing BGP advertisements.
Simple Cisco IOS example:
#configure t (config)#router bgp 65000 (config-router)#address-family ipv4 (config-router-af)#neighbor 169.254.61.206 prefix-list Router-To-Transit-GRE out (config-router-af)#neighbor 169.254.173.78 prefix-list Router-To-Transit-GRE out
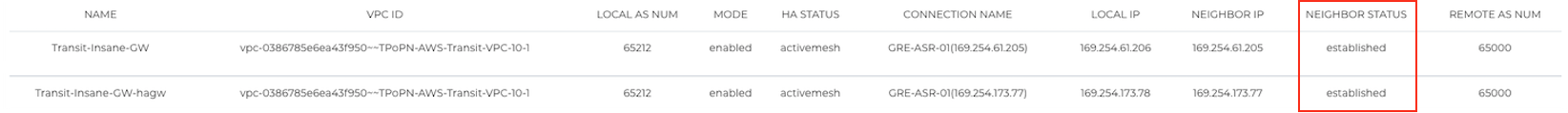
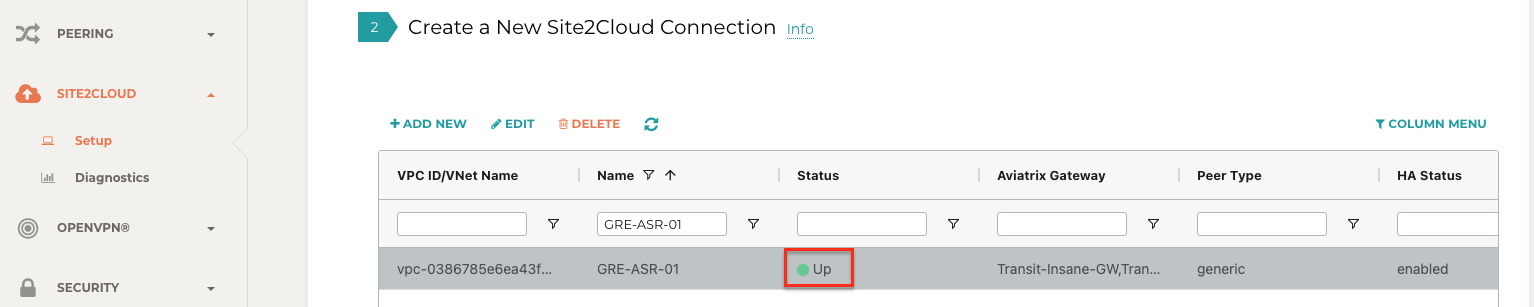
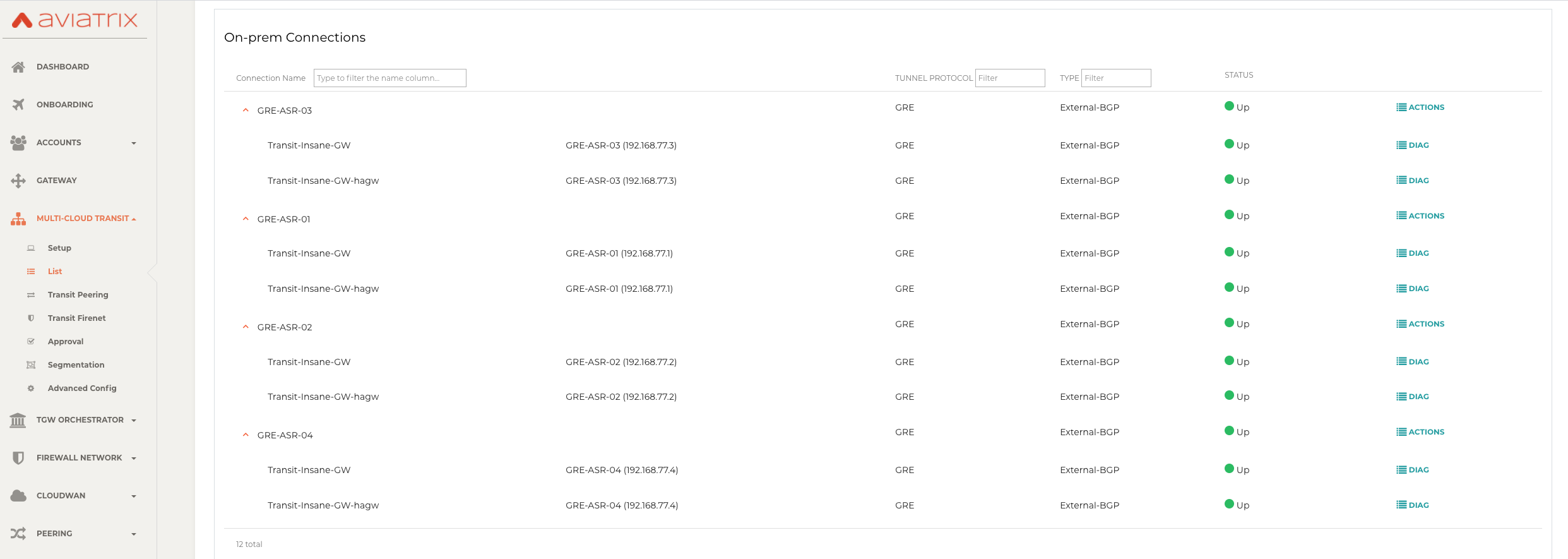
Verifying GRE Tunnel Status on Aviatrix Controller
-
Navigate back to Aviatrix Controller and open Site2Cloud > Setup.
-
Find the connection that you created with Connection Name in the previous step.
-
Check the Tunnel Status.
-
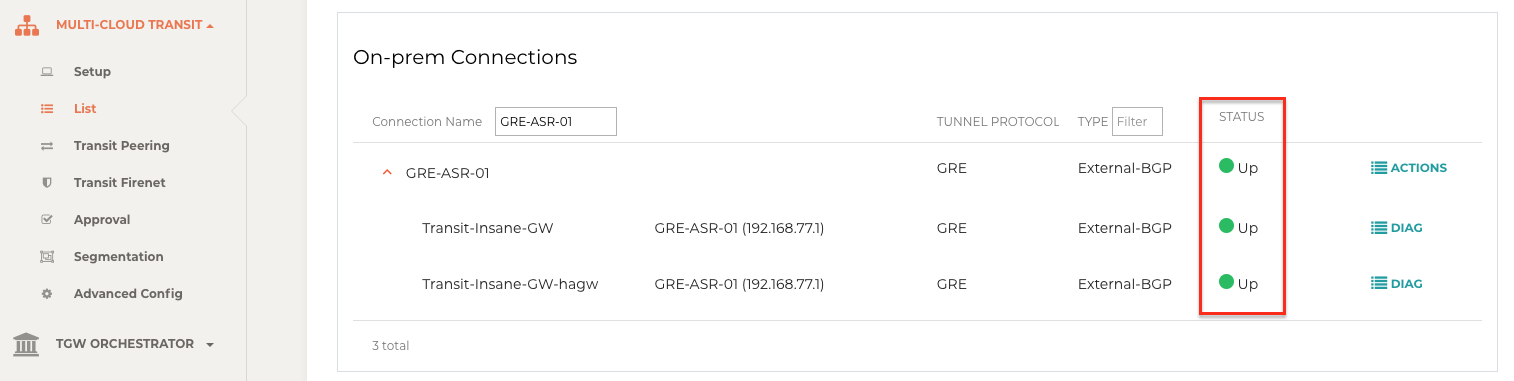
Go to Multi-Cloud Transit > List.
-
Select the Transit Primary Gateway that was created in the previous step.
-
Click Details/Diag.
-
Scroll down to Connections > On-prem Connections.
-
Find the connection that you created with Connection Name in the previous step and check the Tunnel Status.
Configuring ECMP Load Balancing for High Performance
Building Multiple GRE tunnels between Edge Router and Aviatrix Transit Gateway
-
Building multiple GRE tunnels by repeating Build connectivity between edge router and Aviatrix Transit Gateway.
-
Build multiple BGP over GRE tunnels by repeating Build GRE tunnel and BGP over GRE.
In this example, we build up to 4 pairs of GRE connections (total up to 8 tunnels) to benchmark performance.
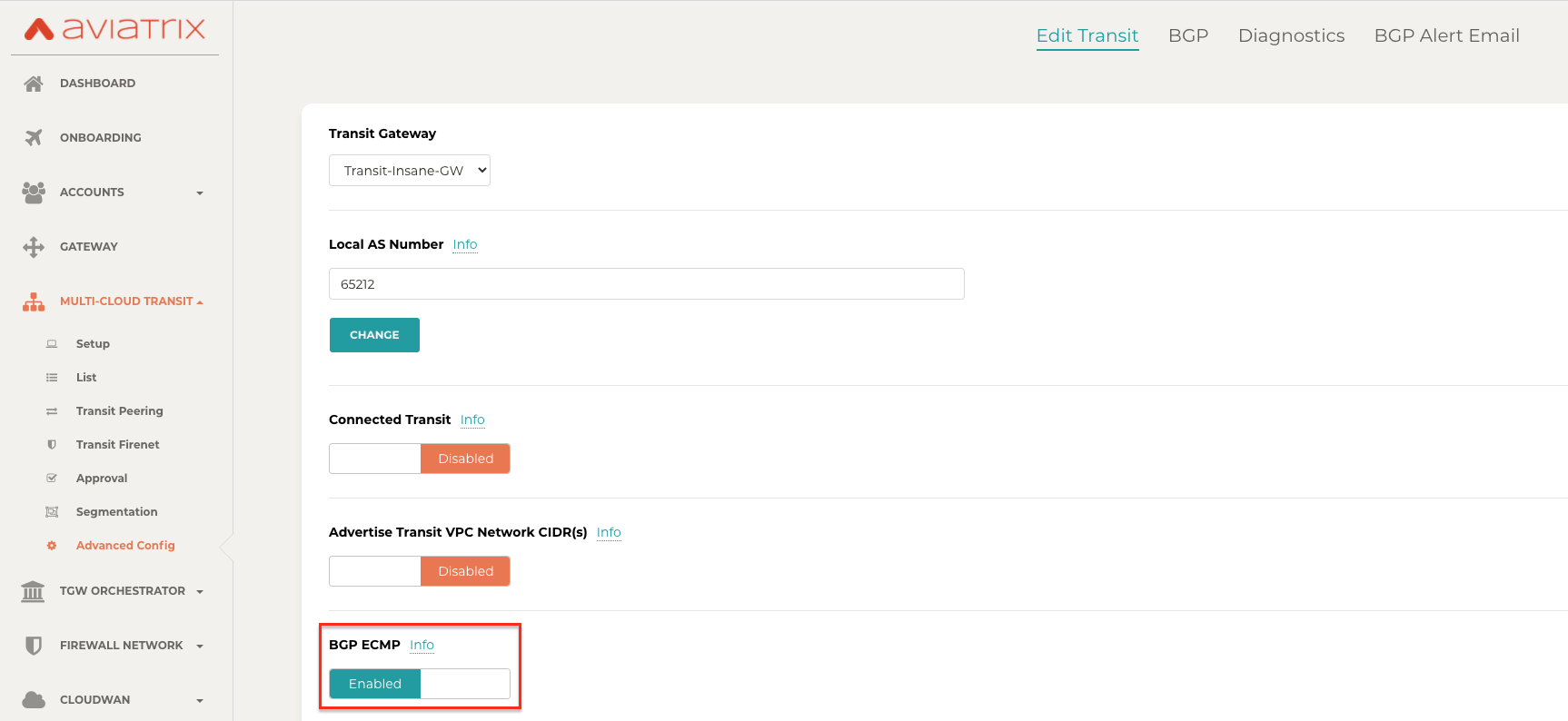
Enabling BGP ECMP feature on Aviatrix Transit Gateway
-
Navigate back to Aviatrix Controller
-
Go to Multi-Cloud Transit > Advanced Config > Edit Transit Tab.
-
Select the Transit Gateway that was created in the previous step.
-
Scroll down to BGP ECMP and enable it.
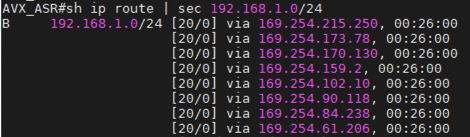
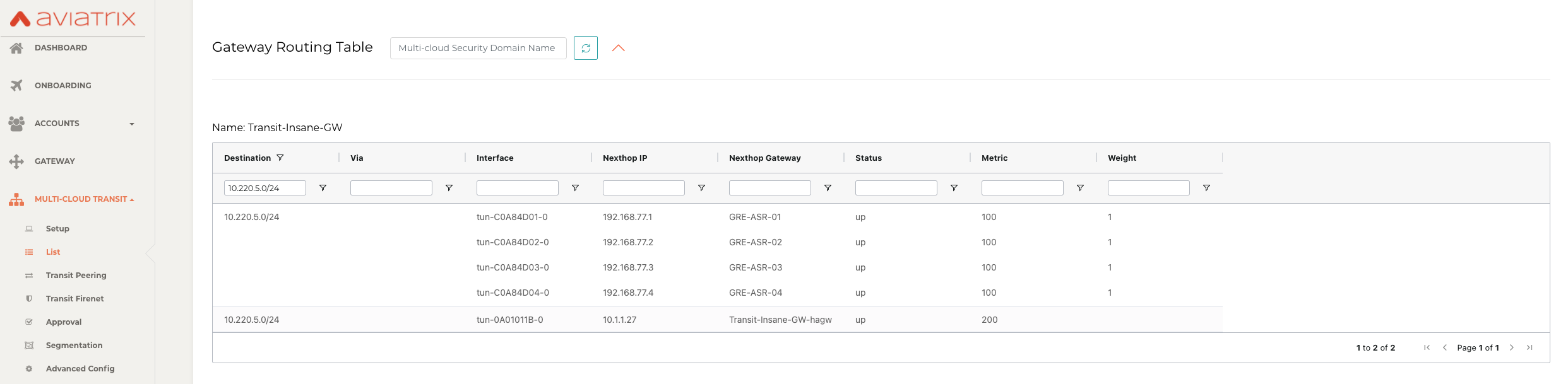
Verifying BGP ECMP feature on Aviatrix Controller
-
Go to Multi-Cloud Transit > List.
-
Select the Transit Primary Gateway that was created in the previous step.
-
Click DETAILS/DIAG.
-
Scroll down to Gateway Routing Table.
-
Click Refresh.
-
Search for the on-prem CIDR in the Destination column.
-
Check whether there are multiple GRE tunnels with same Metric and Weight under the same route entry.
Enabling the BGP ECMP feature on Edge Router
Configure "maximum-paths" with higher number of equal-cost routes in BGP settings so that BGP will install in the routing table. In this example, we configure "maximum-paths 8" to achieve high performance over multiple GRE tunnels.
Simple Cisco IOS example:
#configure t (config)#router bgp 65000 (config-router)#address-family ipv4 (config-router-af)#maximum-paths 8
-
Modify ECMP Load Balancing algorithm depending on traffic type.
Simple Cisco IOS example:
#configure t (config)#ip cef load-sharing algorithm include-ports source destination
Ready to Go
At this point, run connectivity and performance test to ensure everything is working correctly.