About VPN Gateway Settings
VPN Access
When this option is selected, the Aviatrix Gateway will be used for SSL VPN termination. It supports OpenVPN® client and Aviatrix SAML client. For more details, see Aviatrix OpenVPN®.
VPN CIDR Block
When a VPN user connects to the VPN gateway, the user will be assigned a virtual IP address from a pool of IP addresses. This pool of IP addresses is defined as the VPN CIDR Block. The default IP address pool is 192.168.43.0/24.
The only reason you would want to change this address pool is if 192.168.43.0/24 overlaps with your desktop or laptop network address range. For example, if you are on a LAN with a network CIDR 10.0.0.0/24, your desktop IP address will never conflict with your VPN virtual IP address. On the other hand, if your desktop is on a LAN with a network CIDR 192.168.20.0/16, your VPN virtual IP address might conflict with your LAN address. In this case, change the VPN CIDR Block to a different address range, for example, 10.10.0.0/24.
Note a /24 VPN CIDR block supports about 64 simultaneous VPN clients. This is because for each connected VPN client, VPN gateways reserves 3 virtual addresses. For larger number of clients per VPN gateway, consider making the VPN CIDR block to a /22 or /20 network.
Enable SAML
When SAML is enabled, a VPN client/user authenticates to an identity provider (IDP) directly, instead of the gateway doing it on behalf of the user.
In this case, you must use Aviatrix VPN Clients.
Check out the details on how to configure and use Aviatrix VPN Clients for SAML.
MFA Authentication
You can select either Duo or Okta for the VPN gateway to authenticate to these two services on behalf of a VPN user.
When either option is selected, you can use native OpenVPN® client software such as Tunnelblick for iOS and OpenVPN for Windows.
To configure Duo, see How to configure Duo.
To configure Okta, see How to configure Okta.
Max Connections
Maximum number of active VPN users allowed to be connected to this gateway. The default is 100.
When you change this address, make sure the number is smaller than the VPN CIDR block.
The OpenVPN® VPN CIDR Block allocates 4 IP addresses for each connected VPN user; when the VPN CIDR Block is a /24 network, it supports about 60 users.
Split Tunnel Mode
Split Tunnel Mode is enabled by default. When Split Tunnel mode is enabled, only traffic that is destined to the VPC/VNet CIDR where the VPN gateway is deployed is going into the VPN tunnel when a user is connected to the VPN gateway.
When Split Tunnel Mode is disabled (Full Tunnel Mode), all laptop traffic, including Internet traffic (such as a visit to www.google.com), is going through the VPN tunnel when a user is connected to the VPN gateway.
Disabling Split Tunnel Mode should be a deliberate decision. You will be charged for all Internet traffic as they are considered egress traffic by the Cloud Service Provider (AWS/Azure/GCP/OCI).
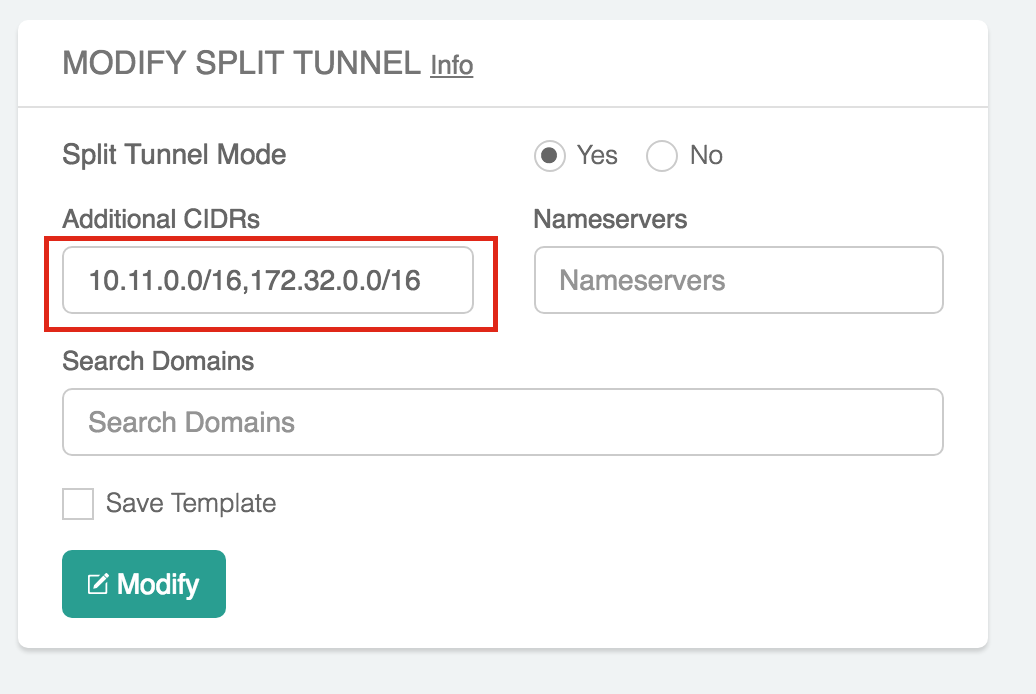
Additional CIDRs
This is an optional parameter. The VPC/VNet CIDR where the VPN gateway is deployed is the default CIDR that VPN gateway pushes to the VPN client. Leave it blank if you do not need it.
When Split Tunnel Mode is enabled, the Additional CIDRs specifies a list of destination CIDR ranges that will also go through the VPN tunnel.
This is a useful field when you have multiple VPC/VNets that the VPN user needs to access.
Enter all network ranges in CIDR blocks separated by commas, as shown below:
|
Nameservers (Optional)
This is an optional parameter. Leave it blank if you do not need it.
When Split Tunnel Mode is enabled, you can instruct the VPN gateway to push down a list of DNS servers to your desktop, so that a VPN user is connected, it will use these DNS servers to resolve domain names.
Search Domains (Optional)
This is an optional parameter. Leave it blank if you do not need it.
When Split Tunnel Mode is enabled, Search Domains lets you specify a list of domain names that will use the Nameserver when a specific name is not in the destination.
Windows VPN clients support a maximum of 10 search-domain entries (the OpenVPN service supports only up to 10 on the Windows OS).
Enable ELB
"Enable ELB" is turned on by default.
When ELB is enabled, the domain name of the CSP’s load balancer (ELB/ALB/CLB), will be the connection IP address when a VPN user connects to the VPN gateway. This connection IP address is part of the .ovpn cert file the Controller sends to the VPN client. Even when you delete all VPN gateways, you can re-launch them without having to reissue a new .ovpn cert file. This helps reduce friction to VPN users.
When the ELB option is enabled, you can launch multiple VPN gateways behind ELB, thus achieving a scale out VPN solution.
ELB Name
The ELB Name is generated automatically if it is left blank. If it is left blank and there is already a load balancer in the specified VPC/VNet, the system uses that load balancer’s name.
You can set the ELB name if there is no existing ELB in the specified VPC/VNet.
VPN Protocol
When the TCP checkbox is marked, the VPN gateway will accept the VPN TCP connection only.
If the UDP checkbox is marked, only the VPN UDP connection is allowed. These options are only available on the AWS.
For all cloud types, the VPN protocol is TCP by default if ELB is enabled. If the ELB is disabled, the VPN protocol is always UDP.
Enable Client Certificate Sharing
This setting is disabled by default.
By enabling the client certificate sharing, all VPN users share one .ovpn file. You must have MFA (such as SAML, DUO + LDAP) configured to make VPN access secure.
Enable Duplicate Connections
This setting controls whether users sharing the same common name can connect at the same time to the VPN Gateway.
If this is disabled, when a user attempts to connect to the gateway through a different device, his existing VPN connection from the current device gets disconnected.
| Users can still land on different VPN Gateways under a load balancer, even though this feature is enabled. |
Enable Policy Based Routing (PBR)
Policy Based Routing enables you to route VPN traffic to a different subnet with its default gateway.
By default, all VPN traffic is NATed and sent to VPN gateway’s eth0 interface. If you want to force the VPN traffic to go out on a different subnet other than VPN gateway eth0 subnet, you can specify a PBR Subnet in the VPC and the PBR Default gateway.
One use case for this feature is Anonymous Internet Surfing.
Enable LDAP
When LDAP authentication is enabled, the VPN gateway will act as a LDAP client on behalf of the VPN user to authenticate the VPN user to the LDAP server.
Set a minimum Aviatrix VPN client software version that is allowed to connect successfully. To configure, go to OpenVPN > Edit Config > MINIMUM VPN CLIENT VERSION to set the Aviatrix VPN client version.
Available for Aviatrix VPN client only.
Enable VPN NAT
This feature controls whether the VPN connection uses NAT (Network Address Translation) while the VPN traffic leaves the Aviatrix VPN Gateway.
VPN NAT is enabled by default. If you want to disable it, you can do so from OpenVPN > Edit Config > VPN NAT.
If NAT is disabled, the traffic would appear to originate from the virtual IP of the VPN user rather than the VPN Gateway itself. Note that you would need to open up the security groups of the target instance to the VPN CIDR for the traffic to flow through. Any peering connection to this VPN gateway would additionally require traffic for the VPN CIDR to be forwarded to the gateway as well.
If you have multiple gateways under the load balancer, you would also need to ensure that the VPN CIDR of the gateways do not overlap, so that the traffic can be routed back to the respective gateway.