Onboarding your GCP Account
Introduction
Before creating a cloud account for GCloud/GCP on the Aviatrix Controller, follow the steps below to make sure you have the credentials set up for API calls.
1. Create a GCloud or GCP account (https://cloud.google.com/). Continue to the next step if you have already done so.
|
The Controller supports multiple accounts with each account associated with a different GCloud projects, but there needs to be at least one account to start with. |
2. Create a GCloud Project.
Enabling Compute Engine API on the Selected Project
-
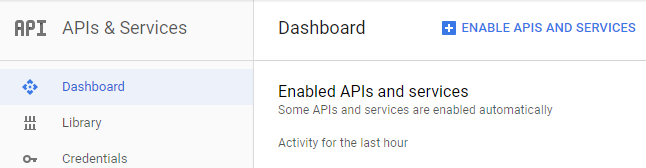
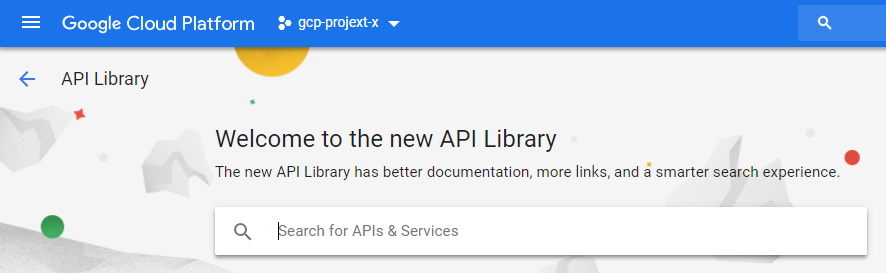
Go to your Google Cloud Platform console, click on the dropdown menu in the top left, and select APIs and Services. At the Dashboard, click Enable APIs and Services.
-
In the Search box, enter "Compute Engine API" and select it from search results.
-
Click Enable.
Creating a Credential File
When you create a cloud account on the Aviatrix Controller for GCloud, you will upload a GCloud Project Credentials file. Follow the steps below to download the credential file from the Google Developer Console.
-
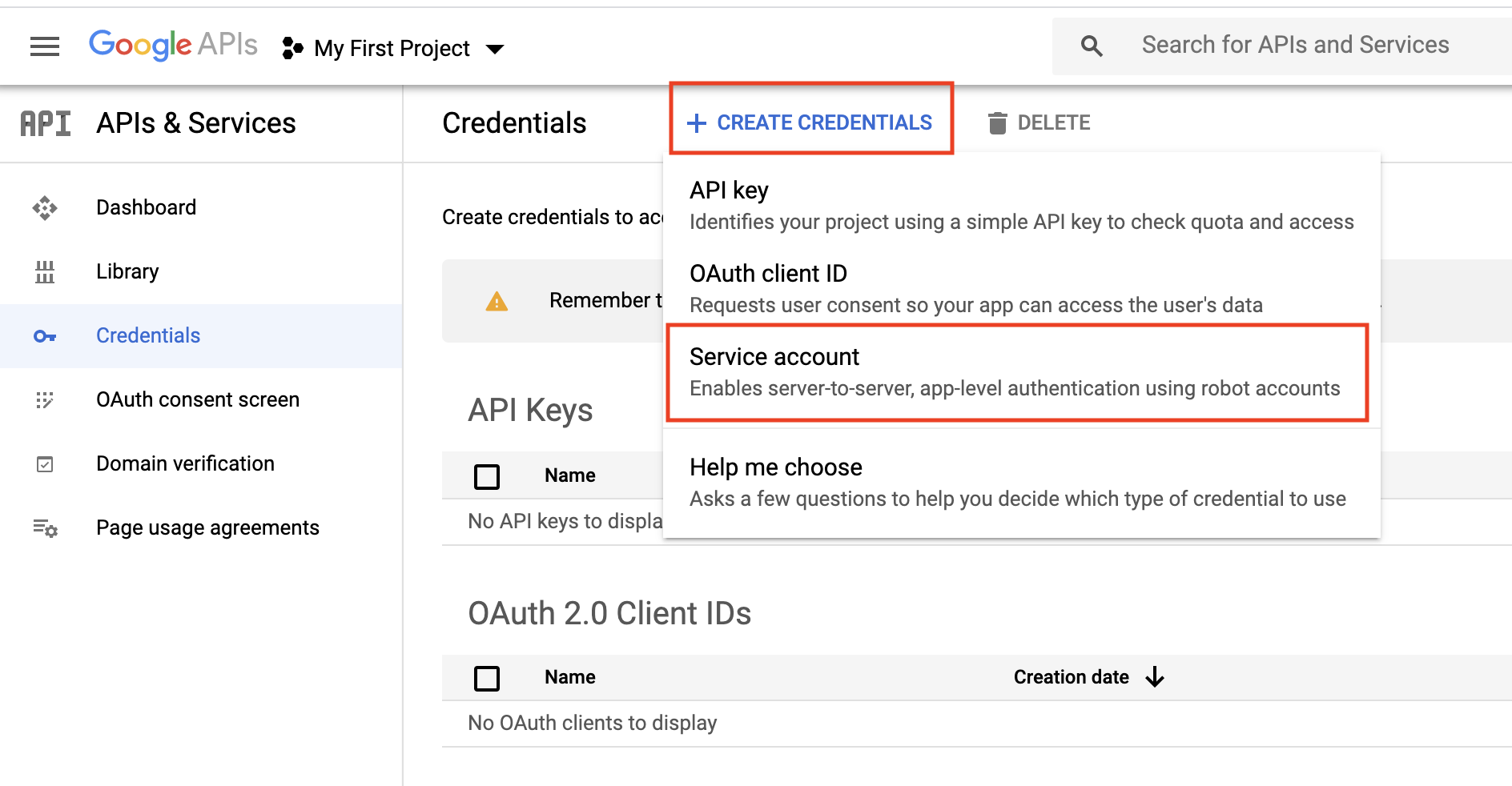
Open the Credential page.
-
Select the project you are creating credentials for.
-
At Credentials, click Create credentials and select Service account as shown below.
-
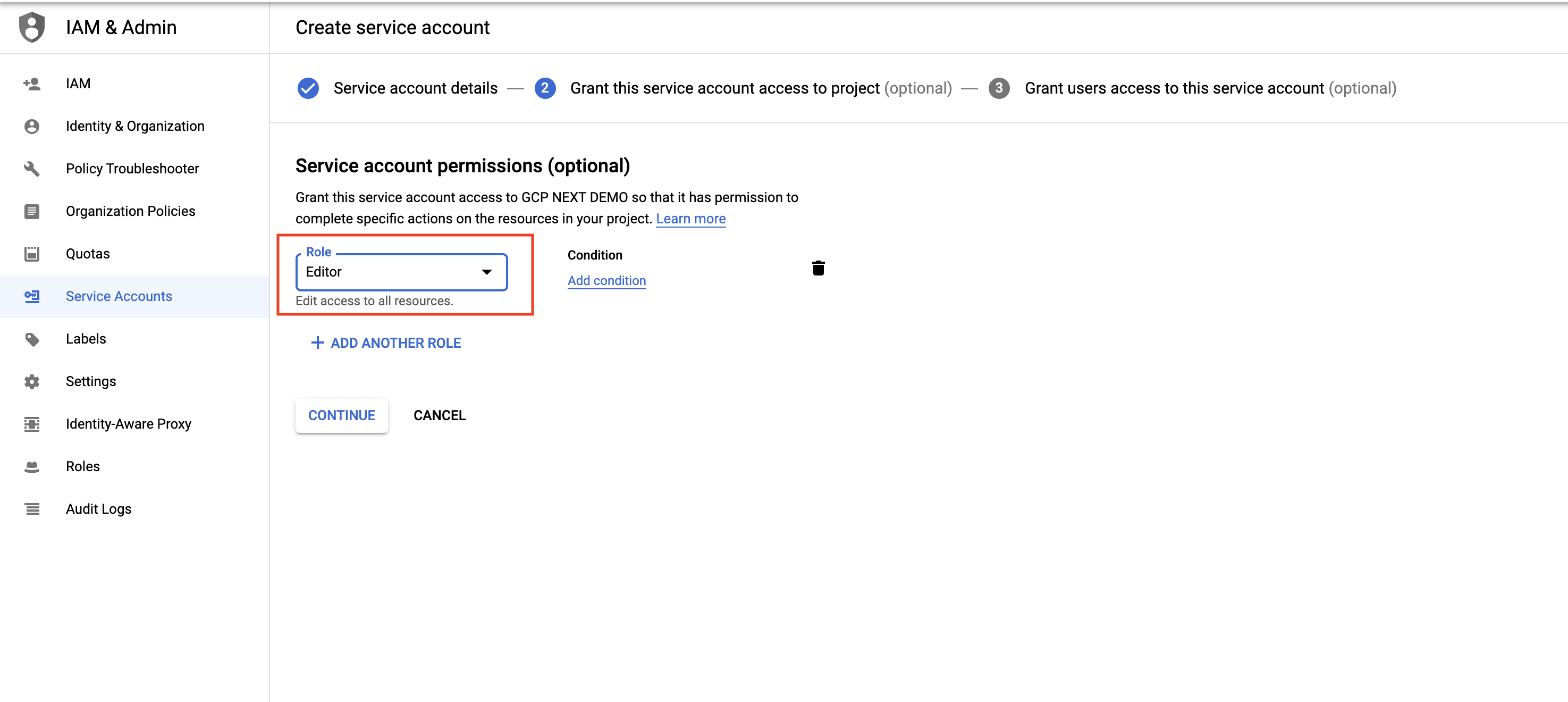
At the Service Accounts, enter a service account name and click Create. For Service account permissions, select Project, Editor, as shown below.
-
Select a service account. Select the Keys tab and click the Add Key dropdown menu, and select Create new key.
-
Select the JSON radio button and click Create.
-
Click Create. The credential file downloads to your local computer.
-
Upload the Project Credential file to the Aviatrix Controller at the Gcloud account create page.
Creating a Service Account with Restricted Access
We recommend creating the service account with the Editor role as mentioned, but in some cases an organization might want to further restrict permission for the service account. In such a situation Aviatrix recommendation is to have at least following roles assigned to service account so that Aviatrix can perform its functions properly, such as managing the compute resources, route tables, firewall rules, shared service VPC network, etc.
-
Compute Admin
-
Service Account User
-
Organization Administrator (required for GCP Shared VPC)
-
Project IAM Admin (required for GCP Shared VPC)
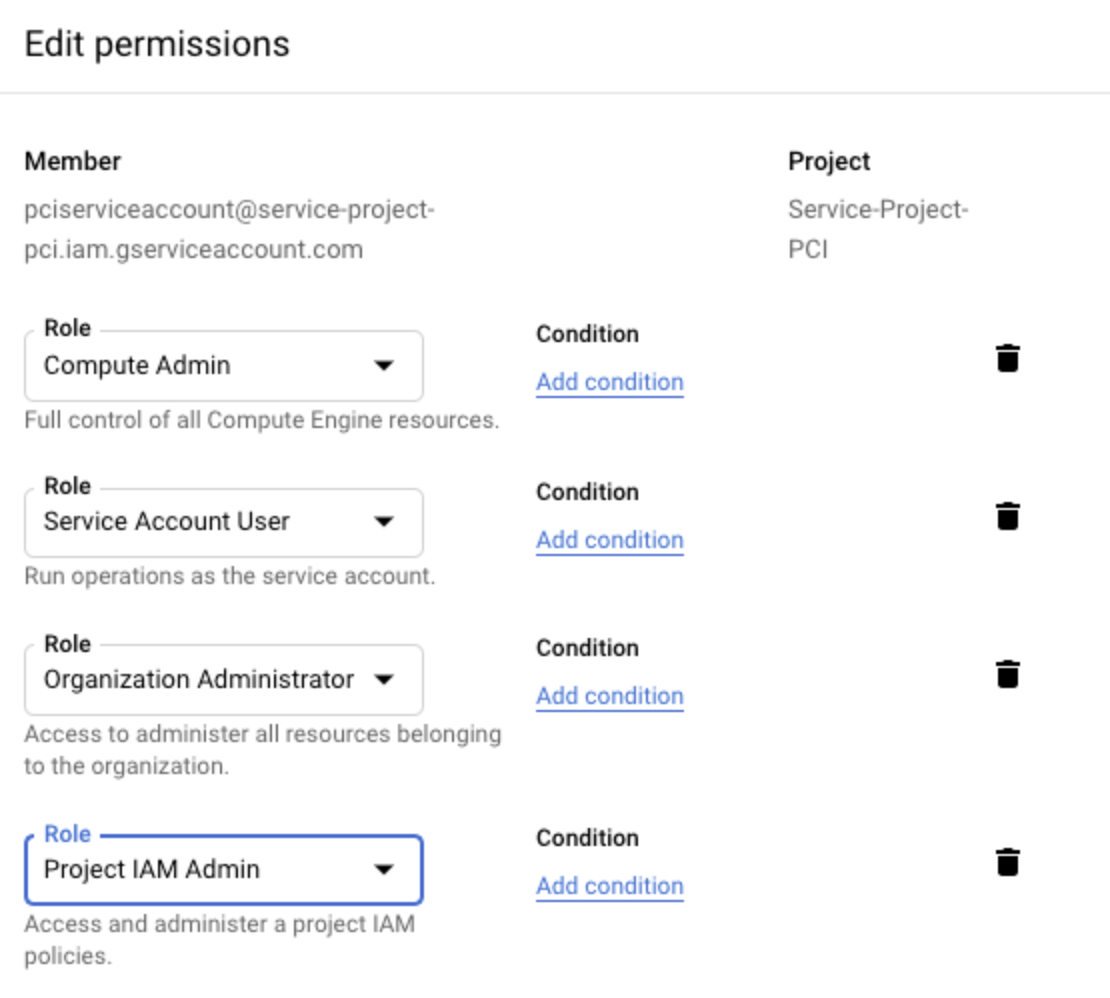
If an organization is currently using GCP Shared VPC or planning to use in future, then enabling Organization Administrator and Project IAM Admin is also required.
In addition to restricting the GCP roles, you can restrict the rights for those roles. You can grant roles permission to perform the following tasks:
compute.addresses.create compute.addresses.createInternal compute.addresses.delete compute.addresses.deleteInternal compute.addresses.get compute.addresses.list compute.addresses.use compute.addresses.useInternal compute.disks.create compute.disks.get compute.firewalls.create compute.firewalls.delete compute.firewalls.get compute.firewalls.list compute.firewalls.update compute.forwardingRules.create compute.forwardingRules.delete compute.forwardingRules.list compute.globalOperations.get compute.healthChecks.create compute.healthChecks.delete compute.healthChecks.useReadOnly compute.httpHealthChecks.create compute.httpHealthChecks.get compute.httpHealthChecks.useReadOnly compute.images.list compute.images.useReadOnly compute.instanceGroups.create compute.instanceGroups.delete compute.instanceGroups.get compute.instanceGroups.update compute.instanceGroups.use compute.instances.create compute.instances.delete compute.instances.get compute.instances.list compute.instances.setDeletionProtection compute.instances.setMachineType compute.instances.setMetadata compute.instances.setTags compute.instances.start compute.instances.stop compute.instances.updateNetworkInterface compute.instances.use compute.networks.addPeering compute.networks.create compute.networks.delete compute.networks.get compute.networks.list compute.networks.removePeering compute.networks.updatePolicy compute.projects.get compute.projects.setCommonInstanceMetadata compute.regionBackendServices.create compute.regionBackendServices.delete compute.regionBackendServices.get compute.regionBackendServices.update compute.regionBackendServices.use compute.regionOperations.get compute.routes.create compute.routes.delete compute.routes.list compute.subnetworks.create compute.subnetworks.delete compute.subnetworks.get compute.subnetworks.list compute.subnetworks.use compute.subnetworks.useExternalIp compute.targetPools.addInstance compute.targetPools.create compute.targetPools.delete compute.targetPools.get compute.targetPools.removeInstance compute.targetPools.use compute.zoneOperations.get compute.zones.list iam.serviceAccounts.actAs logging.logEntries.create pubsub.subscriptions.consume pubsub.subscriptions.create pubsub.subscriptions.delete pubsub.subscriptions.get pubsub.topics.attachSubscription pubsub.topics.create pubsub.topics.delete pubsub.topics.get pubsub.topics.publish resourcemanager.projects.get
Onboarding your GCP Account in Your Controller
To onboard this GCP account into your Aviatrix Controller, use the following steps.
-
Open your Controller and go to Onboarding > click Google Cloud Platform.
-
Under Enter Aviatrix Customer ID, enter the customer ID you received in an email.
-
Skip the Enter Certificate Domain field.
-
Under Create Primary Access Account, enter the following information.
| Parameter | Description |
|---|---|
Account Name |
Enter a clear Account Name. |
Gcloud Project ID (Optional) |
In the Gcloud Project ID field, enter the name of the Gcloud project for this account. |
Gcloud Project Credentials |
Click Choose file and choose the correct JSON file downloaded from your GCP account. |
-
Click Create.
Onboarding Multiple GCP Service Accounts
The Controller supports multiple Service Accounts from different GCloud projects. Onboard each GCP account separately using a unique Account Name, the correct Project ID for each project, and the JSON credentials file from the main Management Account.
For example, you may need to set up a Service Account in the first or Management GCP Project, and then give that Service Account access to a second Gcloud Project where they can deploy gateways.
-
First, in your GCP account, create the first or Management Project and the secondary project.
-
Create a Service Account from within the Management Project.
-
Generate a JSON file from the Management Project. This JSON file is the credentials file you will use while onboarding this account in your Controller.
-
Give this Service Account permission to access the secondary project.
-
Log into your Controller and go to Onboarding > Google Cloud Platform. Enter a clear Account Name, use the Management Project Name as the Gcloud Project ID, and upload the JSON credentials file. Click Create.
-
Now, onboard the secondary account. Enter a clear Account Name that helps you distinguish these projects, use the secondary project’s ID as the Project ID, and upload the same JSON credentials file from the Management Project. Click Create.
Now, your Controller has access to the Management Project and the secondary project where you can deploy gateways.