Controller Backup and Restoration
Overview
When deployed in a cloud environment, the Aviatrix Controller is not in the data path as packet processing and encryption is done by the Aviatrix gateways.
When the Controller is down or out of service, your network will continue to be operational and encrypted tunnels and OpenVPN® users stay connected and are not affected. Since most of the data logs are forwarded from the gateways directly, the loss of log information from the Controller is minimal. The only impact is that you cannot build new tunnels or add new OpenVPN® users.
This loosely coupled relationship between the Controller and gateways reduces the impact of the availability of the Controller and simplifies your infrastructure. Since the Controller stores configuration data, it should be periodically backed up to the appropriate AWS/Azure/Google account. If a replacement Controller is launched, you can restore the configuration data from your backup.
|
Before stopping your existing Controller:
|
Backing up Your Configuration
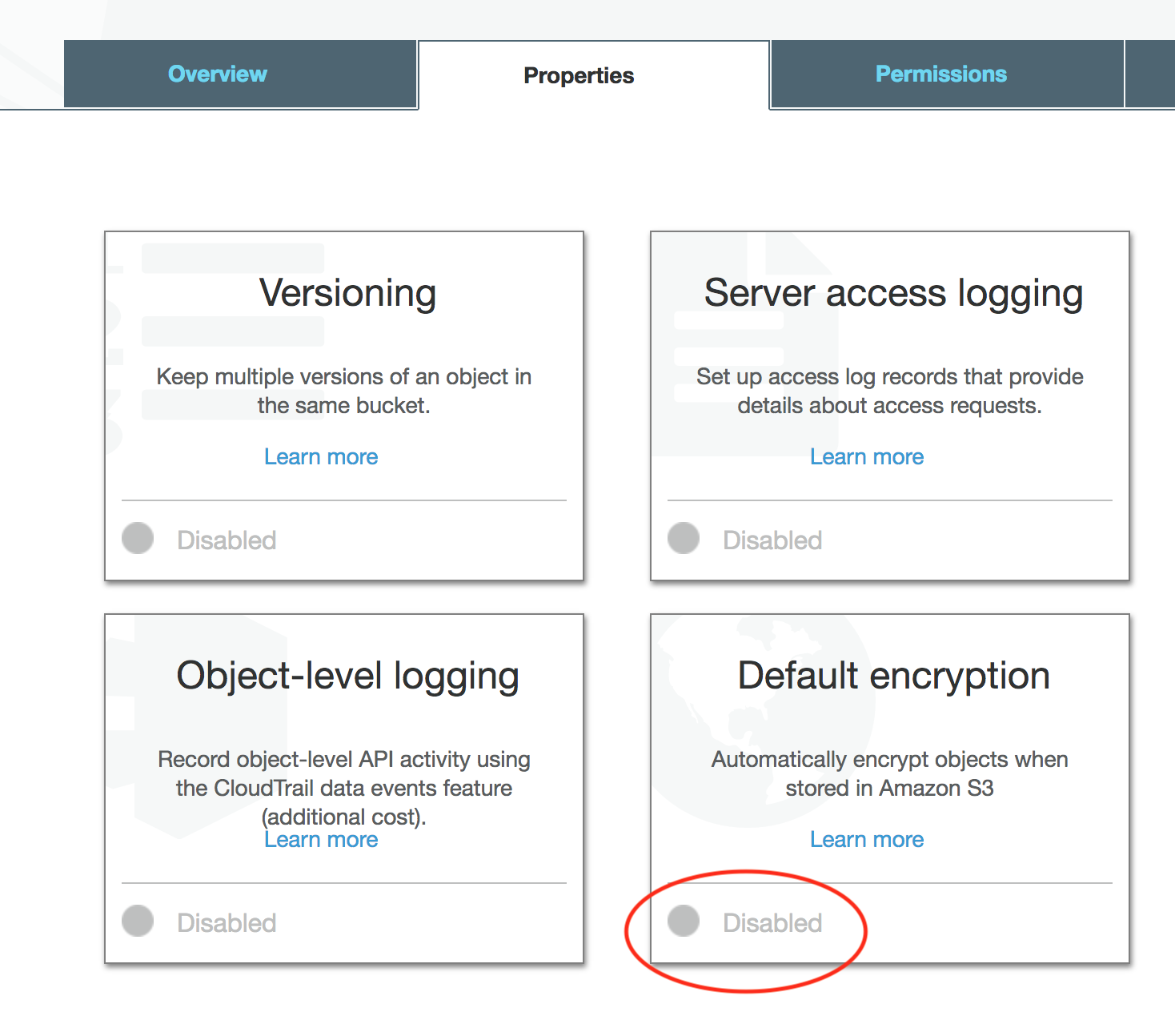
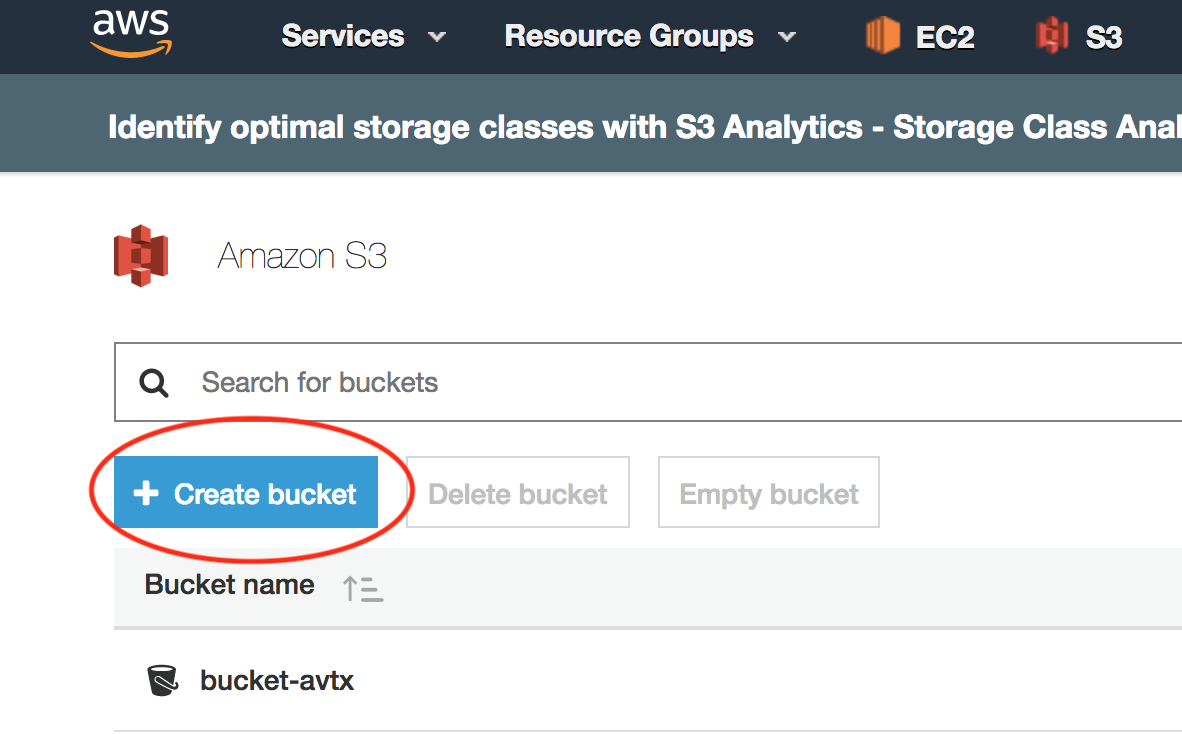
Aviatrix stores the Controller backup in an AWS S3 bucket or an Azure Container. Before you begin, determine where you would like to store the backup and create either the S3 bucket or Azure Container.
|
-
Log into the Controller.
-
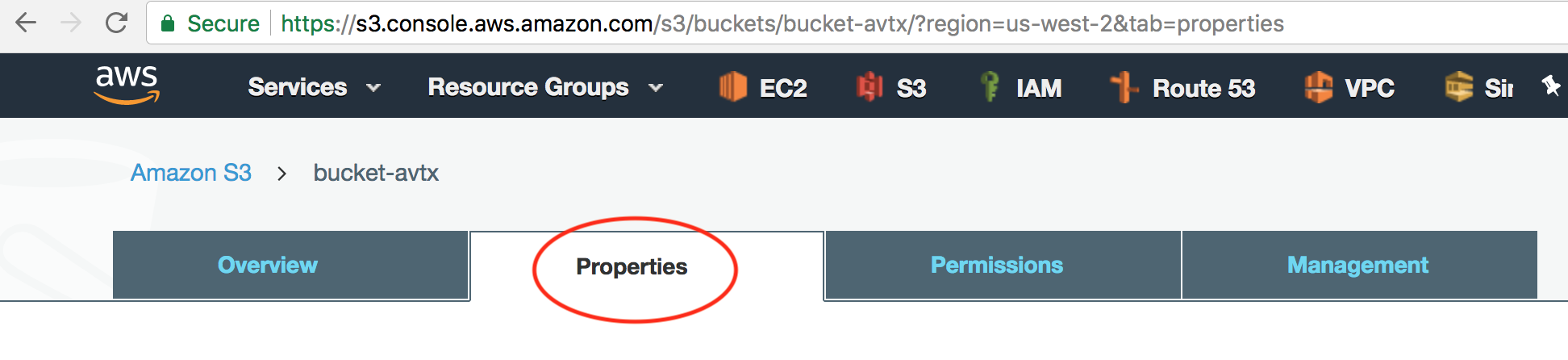
Go to Settings > Maintenance > select the Backup & Restore tab.
-
Under the Backup section:
-
Select the appropriate Cloud Type and Account Name.
-
Populate the S3 Bucket Name for AWS or Region, Storage Name, and Container Name for Azure.
By default, only the latest configuration data is stored. Each time the configuration is backed up, it overwrites the previous one. If you would like to keep every copy, check the box Multiple Backup.
-
-
Click Enable.
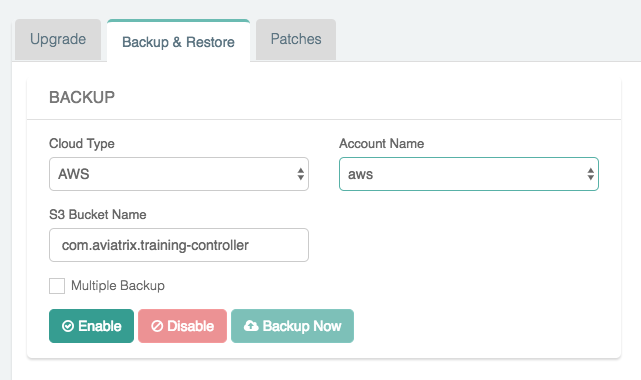
The first time you enable this feature, the configuration will backed up to your specified location. After this, the configuration data is automatically backed up daily at 12 am.
Selecting the Multiple Backup checkbox enables the Controller to backup up to a maximum of 3 rotating backups. Each backup filename will contain the date and time of when the backup is made. Additionally, the backup without any date and time in the filename contains a copy of the latest backup.
If you want to force an immediate backup (e.g. for a configuration change) you can accomplish this by clicking Backup Now. If multiple backups are not enabled, each time the configuration is backed up, the backup up file will be overwritten. Otherwise, the oldest backed up will be overwritten.
|
Selecting the Multiple Backup option is recommended. If the backup is already Enabled, go ahead and Disable it, turn on the Multiple Backup option and then Enable the backup again. |
|
You should enable cross-region replication in AWS when creating your S3 buckets. This ensures that an S3 bucket remains accessible if there is a regional CSP failure. The replacement Controller can retrieve and restore its backup file. |
Restoring Your Configuration
|
Make sure your Controller backup and Controller restore take place in the same CSP (Cloud Service Provider): AWS, Azure, or GCP and share the same basic configuration. For example, an AWS backup can only restore to another AWS Controller. Note that in the case of AWS backups, an AWS Controller set up with IAM roles cannot backup and restore to an AWS Controller set up with a secret key, or vice versa. |
If you are starting from a new Controller, follow these steps to get started:
-
Log into the Controller with the admin username and the default password.
-
Follow the initial steps to get the Controller up and running:
-
Shut down the older Controller.
-
Transfer the IP address to the new Controller.
-
Proceed to configure the new Controller by entering an email address.
-
Change your admin password.
-
Enter or skip the proxy configuration.
-
Allow the upgrade to run.
-
Once you are past the initial configuration steps:
-
Log into the Controller.
-
Go to Settings > Maintenance > select the Backup & Restore tab.
-
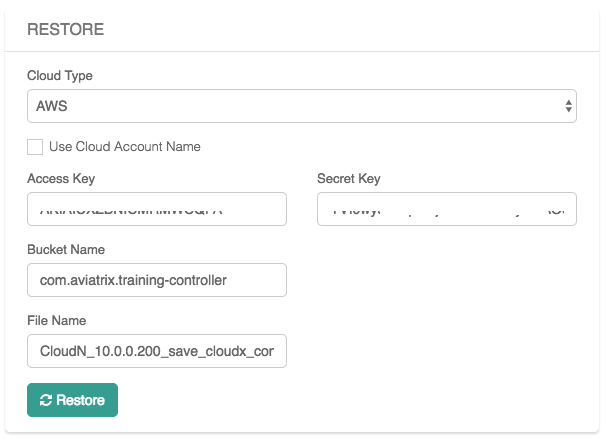
Under the Restore section:
-
Select the Cloud Type:
-
For AWS:
-
If you would like to use an existing account, please make sure you create one Access Account only with the exact Access Account Name that was used in your previous Controller. Mark the Use Cloud Account Name checkbox and select the account. Otherwise, enter an Access Key and Secret Key.
-
Enter the Bucket Name and File Name of the file to restore.
-
-
For Azure:
-
Enter the Subscription ID and Certificate Path.
-
Enter the Storage Name, Container Name, and File Name of the file to restore.
-
-
-
Click Restore.
If Aviatrix Managed CloudN exists in the backup Controller, after the restore operation on the new Controller, you must navigate to the Aviatrix Managed CloudN UI and follow steps of 2.2 and 2.5 in Workflow on Aviatrix CloudN by entering the new FQDN or IP of the new Controller to complete the restore. You must repeat 2.2 and 2.5 on other Aviatrix Managed CloudN devices if you have more than one.
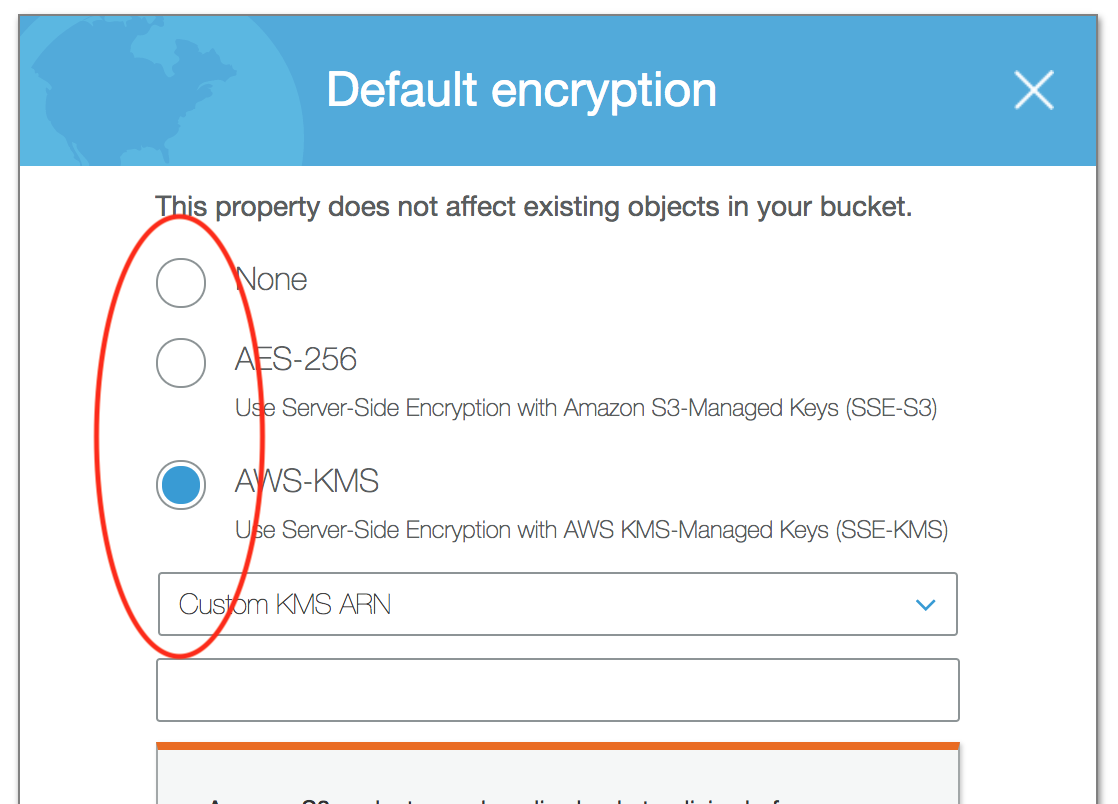
AWS Encrypted Backups
AWS S3 allows uploaded backup files to be encrypted in the server side for more secure storage. The encryption is all done in the AWS S3 server side. This server side secure storage is in addition to the already encrypted Aviatrix Controller backups.
1. Create AWS S3 bucket
4. If AWS-KMS with Custom KMS ARN is selected, additional configuration will be needed:
-
Create a Custom Encryption Key by going to IAM > Encryption Keys > click Create Key.
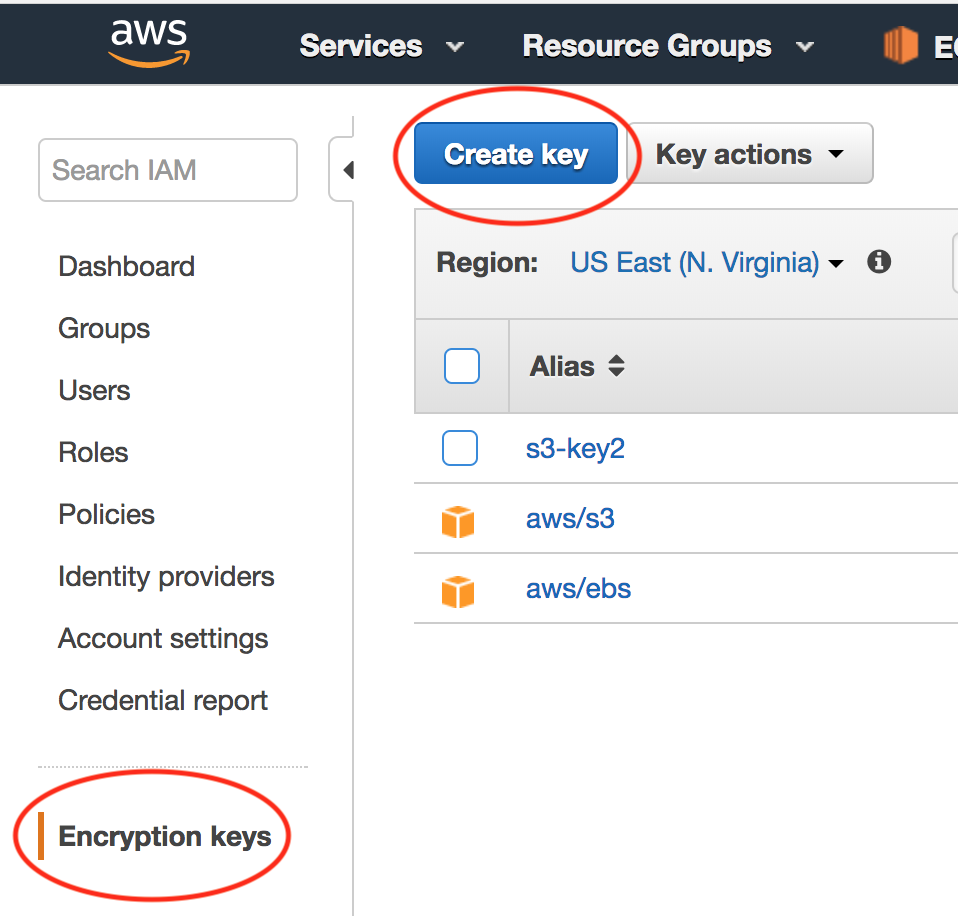
-
Copy the custom Key KMS ARN to the S3 encryption property configuration.
|
Make sure that the custom encryption key and the S3 bucket are in the same region. |
-
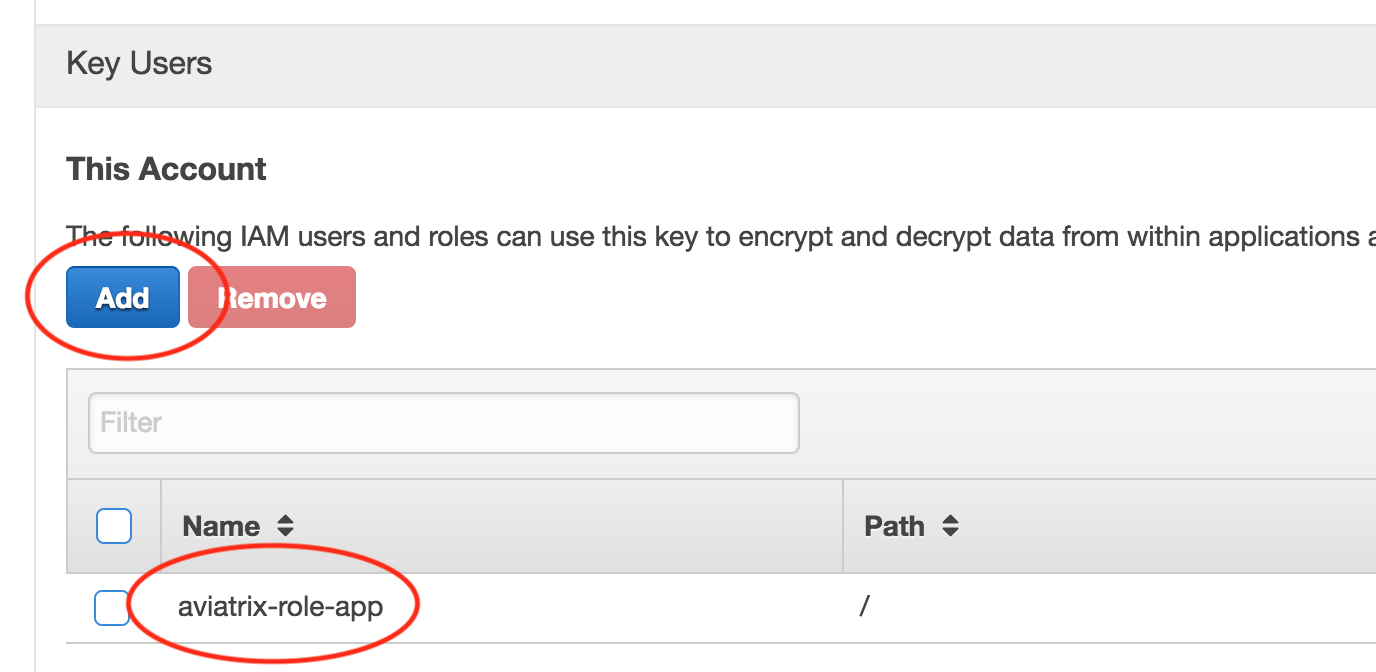
If IAM user is used for onboarding authentication, add user "aviatrix-role-app" into the key.
Azure Private Link Backups
Azure Private Link enables you to access Azure PaaS Services (for example, Azure Storage and SQL Database) and Azure hosted customer-owned/partner services over a private endpoint in your virtual network. Traffic between your virtual network and the service travels the Microsoft backbone network. Exposing your service to the public internet is no longer necessary.
By leveraging the Azure private link, the Controller backups will happen privately from your VNet so that your blob storage account does not need to be exposed to the outside world.
2. Set up the Storage Account for Private Link
-
On the Networking tab for the storage account creation, select Private endpoint for the connectivity method.
-
Add a new private endpoint with the target of the blob storage resource and enable DNS Integration.
|
If you currently have existing private endpoints deployed, you may need to leverage an existing private zone in another subscription. This must be completed through the dedicated private endpoint creation workflow. For additional assistance with this setup please reach out to an Aviatrix Solution Engineer. |