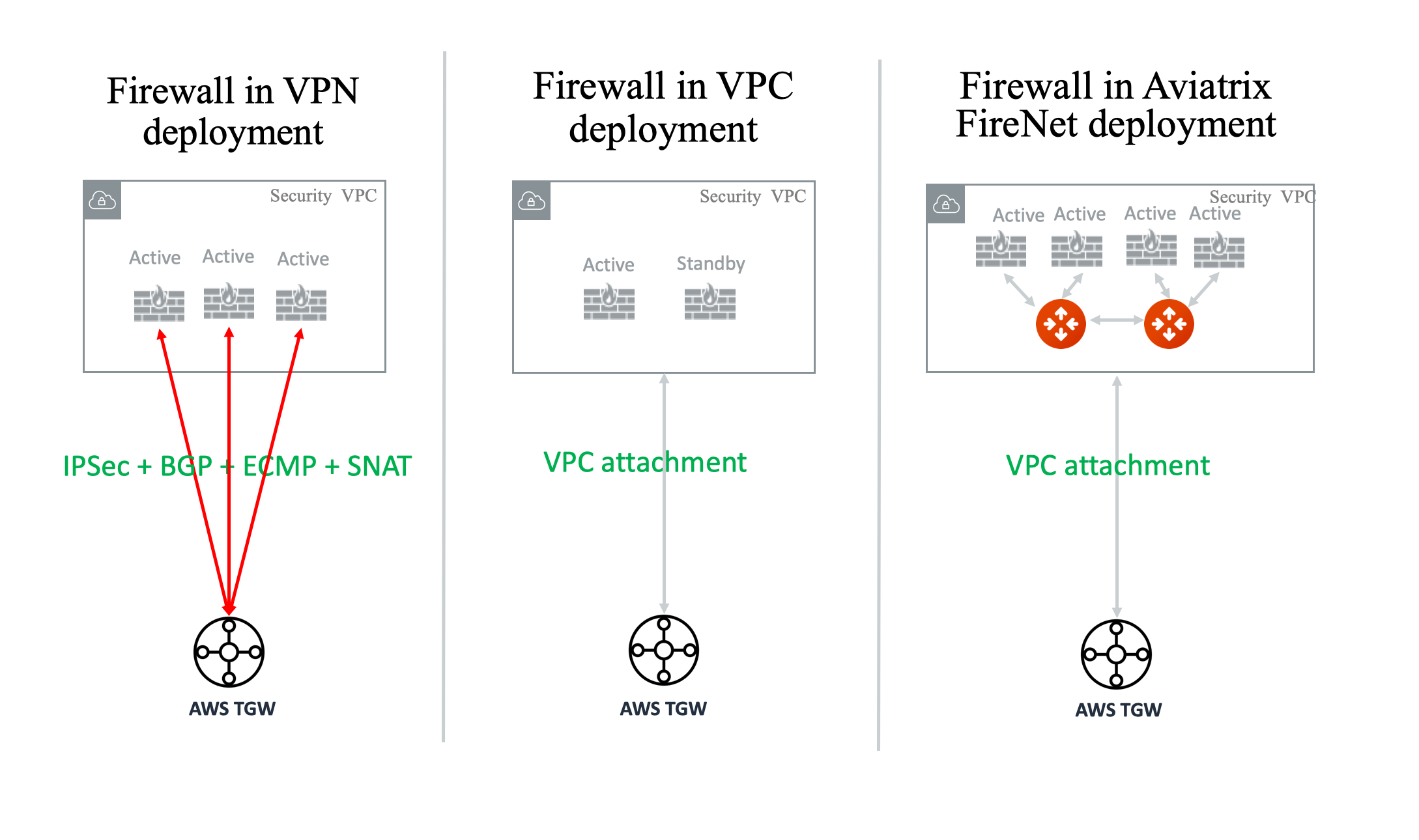
| Firewall Deployment Functions | Firewall in VPN deployment * | Firewall in VPC/VNet attachment * | Firewall in Aviatrix FireNet |
|---|---|---|---|
| On-prem to VPC/VNet traffic inspection | Yes | Yes | Yes |
| VPC/VNet to VPC/VNet traffic inspection | Yes (requires SNAT) | Yes | Yes |
| Egress traffic inspection | Yes | Yes | Yes |
| Per firewall performance | 500Mbps | Up to 6Gbps | Up to 6Gbps |
| Total FireNet performance | > 500Mbps | Up to 6Gbps | up to 75Gbps |
| Multiple firewalls (scale out) | Yes | No (Active/Standby) | Yes |
| Integrated solution | Yes | No (requires external script) | Yes |
| Solution complexity | High | Medium | Low |
| Centrally managed | Yes | No (requires external script) | Yes |
| Multi-vendor support | Yes | Yes | Yes |

