Access Account
The Aviatrix Controller is a multicloud and multi-accounts platform. The Controller uses your cloud provider API credentials to make API calls, for example, to launch an Aviatrix gateway instance, on behalf of your cloud accounts. One cloud credential is represented as an Aviatrix access account on the Controller. The Controller supports multiple Aviatrix accounts. One Aviatrix account can have multiple service accounts from different clouds, one from each cloud. For example, an Aviatrix account named DevOps can have an access account for AWS, Azure ARM credentials, and GCP credentials.- Starting from release 3.2, an access account for AWS only consists of the 12-digit account ID.
- For Azure, the account information consists of Azure ARM credentials.
- For GCP (Google Cloud), the account information consists of GCP Credentials.
- For AWS China, please refer to Account with Access Key.
- Launch Aviatrix Gateways in the VPC/VNets that belong to this account.
- Add access accounts from other Cloud Service Providers. For example, if you launched your Aviatrix Controller through the Azure marketplace, your can add access accounts for AWS, GCP, and OCI.
Setting Up Additional Access Accounts for Different Clouds
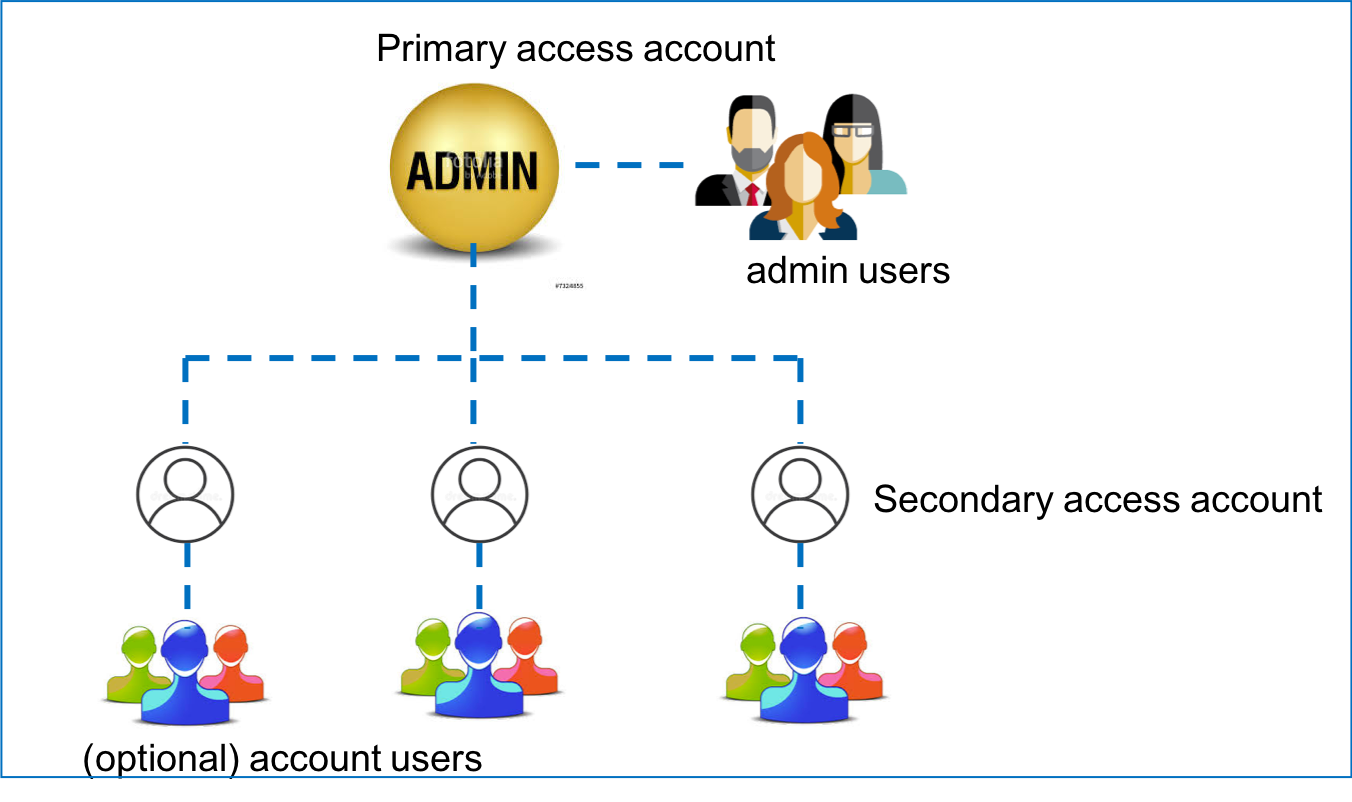
After you go through the onboarding process and create the primary access account, you can create additional Aviatrix access accounts on the Controller. This allows you to launch gateways and build connectivity across different cloud accounts. For example, if you create a primary access account in Azure, where you launched your Controller, you can add additional access accounts for AWS, GCP, and OCI. To launch an additional access account:- Go to your Aviatrix Controller > Accounts > Access Accounts.
- Click + Add New to create this new access account.
- Enter a unique account name: for example, BU-Group-3.
- Mark the radio button for the appropriate Cloud Service Provider. The fields below change based on which Cloud Service Provider you chose. See the following documents for more information on adding access accounts in each cloud:
If you launched your Controller in Azure, GCP, or OCI, leave the IAM roles checkbox unmarked for any additional AWS access accounts.
- After entering the information required, scroll down and select any RBAC or permission groups this account should belong to.
- Click OK.
Account Audit Logs
You can download the full set of logs to audit user access activities:- Go to Administration > Audit page on the CoPilot UI.
- Select a desired time period. Then choose any filters as needed. Click Apply.
- Click the Download icon
 to download the API logs.
to download the API logs.

