Enable the Distributed Cloud Firewall (DCF) feature to avail the WebGroups. See Distributed Cloud Firewall Overview for more information.
To filter HTTP or HTTPS traffic with a URL-based WebGroup, TLS Decryption must be enabled in the rule where the WebGroup is used.Non-TLS or non-HTTP traffic will not match the rule that uses the WebGroup and will be evaluated against later rules.
Considerations
-
A TLS packet with no SNI header will only match the All-Web default WebGroup. You can create a DCF rule that uses a URL-type WebGroup to capture the packet, but only exact match URLs are supported at this time.
As an alternative to using a URL-based WebGroup, you can configure an L4 rule without WebGroups to allow the traffic based on IP address, and insert it before the first L7 rule.
-
For non-TLS encrypted HTTP traffic, there is no SNI header. The following values are used instead:
- Domain-based WebGroups: the value of the HTTP Host Header.
- URL-based WebGroups: the URL value, as it would be for HTTPS (as long as TLS Decryption is enabled).
- Non-TLS, non-HTTP traffic will not match any WebGroup.
-
Full wildcard support is available for both URL and domain-based WebGroups (e.g.,
*.example.com).
System-Defined WebGroup
When you navigate to Security > Distributed Cloud Firewall > WebGroups, a system-defined WebGroup, ‘All-Web’, has already been created for you (if no other WebGroups exist). This predefined WebGroup cannot be deleted.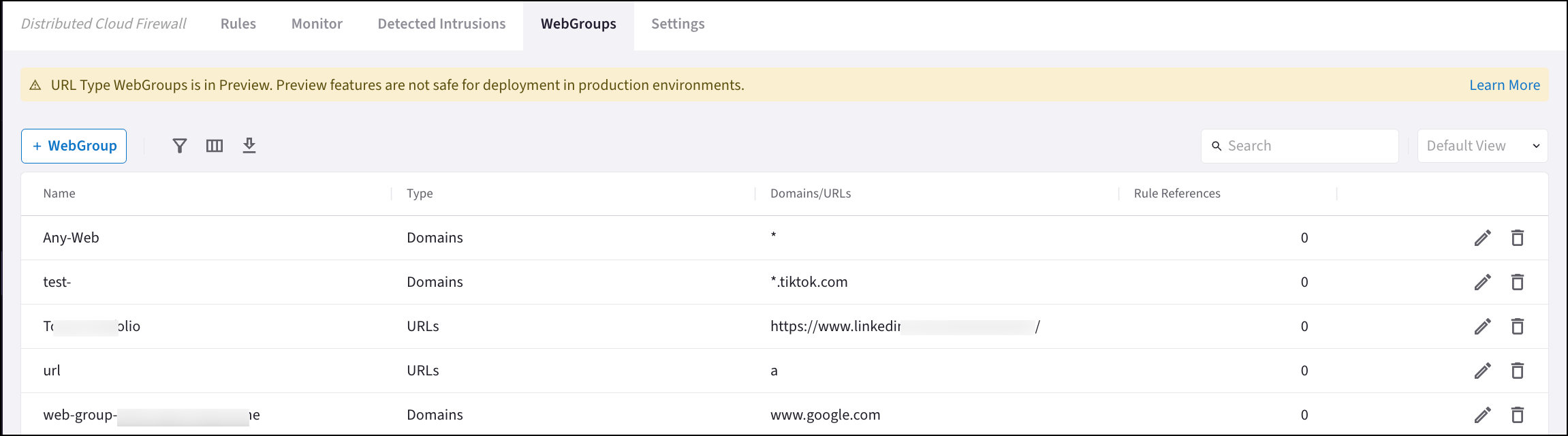
Prior to Release 7.1.3006, the default WebGroup was named ‘Any-Web’ and was created by CoPilot. If you still have this WebGroup, you can modify it (if it is being used by Distributed Cloud Firewall rules) or delete it (if it is not used by any Distributed Cloud Firewall rules) so that it is not confused with the default ‘Any-Web’ WebGroup created by Controller.
SNI Verification
SNI Verification is only present if using Controller 8.0 or later.

